Protecting Against Industrial Espionage
By now, you are aware that there are many ways that your organization’s valuable information assets can be compromised. What steps can you take to alleviate the danger? Note that I said alleviate the danger. There is nothing you can do to make any system, any information, or any person totally secure. Totally unbreakable security is simply unattainable. The best you can do is work to achieve a level of security that makes the effort required to get information more costly than the value of the information.
One obvious protection is to employ antispyware software. As mentioned earlier in this book, many antivirus programs also have antispyware capabilities. This software, coupled with other security measures, such as firewalls and intrusion detection software (examined in Chapter 9, “Computer Security Technology”), should drastically reduce the chance that an outside party will compromise your organization’s data. Furthermore, implementing organizational policies (also discussed in Chapter 9) that help guide employees on safely using computer and Internet resources will make your system relatively secure. If you add to your protection arsenal the strategy of encrypting all transmissions, your system will be as secure as you can reasonably make it. (Chapter 8, “Encryption,” is devoted to encryption.) However, all of these techniques—firewalls, company policies, antispyware, encryption, and so forth—will only help in cases in which the employee is not the spy. What do you do to ameliorate the danger of employees intentionally stealing or compromising information? Actually, there are several courses of action any organization can take to reduce risks due to internal espionage. Here are 12 measures you can use:
Always use all reasonable network security: firewalls, intrusion detection software, antispyware, patches and updates for the operating system, and proper usage policies.
Give the personnel of the company access to only the data that they absolutely need to perform their jobs. This concept is referred to as least privileges. The employees are given the minimum privileges necessary to perform their job tasks. Use a need-to-know approach. One does not want to stifle discussion or exchange of ideas, but sensitive data must be treated with great care.
If possible, set up a system for those employees with access to the most sensitive data in which there is a rotation or a separation of duties. Ensure that no one employee has access and control over all critical data at one time.
Limit the number of portable storage media in the organization (such as CD burners and flash drives) and control access to these media. Log every use of such media and what was stored. Some organizations have even prohibited cell phones because most phones allow the user to photograph items and send the pictures electronically.
Do not allow employees to take documents/media home. Bringing materials home may indicate a very dedicated employee working on her own time or a corporate spy copying important documents and information.
Shred documents and melt old disks/tape backups/CDs. A resourceful spy can often find a great deal of information in the garbage. If any storage media is disposed of, it should be completely wiped. Degaussing is a good technique for hard drives and USB drives.
Do employee background checks. You must be able to trust your employees, and you can only do this with a thorough background check. Do not rely on “gut feelings.” Give particular attention to information technology (IT) personnel who will, by the nature of their jobs, have access to a wide variety of data. This scrutiny is most important with positions such as database administrators, network administrators, and network security specialists.
When any employee leaves the company, scan the employee’s PC carefully. Look for signs that inappropriate data was kept on that machine. If you have any reason to suspect inappropriate usage, then store the machine for evidence in subsequent legal proceedings.
Keep all tape backups, sensitive documents, and other media under lock and key and allow limited access to them.
If portable computers are used, then encrypt the hard drives. Encryption prevents a thief from extracting usable data from a stolen laptop. A number of products on the market can accomplish this encryption, including the following:
VeraCrypt (see Figure 7.5) is one example of a free tool for encrypting drives, folders, or partitions. The tool is remarkably easy to use and can be found at https://www.veracrypt.fr.
There are several other similar tools, most of which are low cost or free.
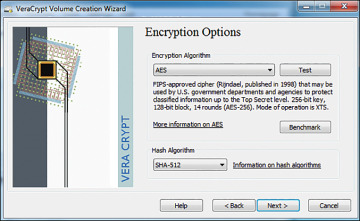
Figure 7.5 VeraCrypt.
Microsoft Windows includes two types of encryption. Windows 7 Enterprise or Ultimate editions included BitLocker for encrypting entire hard drives. BitLocker is also available on later versions of Windows (8, 8.1, 10, 11). And all versions of Windows since Windows 2000 have included Encrypted File System for encrypting specific files or folders (see Figure 7.6).
DiskCryptor is an open-source drive encryption application. It supports algorithms such as AES and Serpent (which you will learn more about in Chapter 8). DiskCryptor can encrypt external devices such as USB and DVD devices. It is available from https://diskcryptor.org.
This list is not exhaustive; therefore, it is highly recommended that you carefully review a variety of encryption products before making a selection.
Have all employees with access to any sensitive information sign nondisclosure agreements. Such agreements give an employer recourse in the event that an ex-employee divulges sensitive data. It is amazing how many employers do not bother with this rather simple protection. Use of nondisclosure agreements is the primary means of protecting trade secrets.
Conduct security awareness sessions. Clearly, employee education is one of the most important things you can do. An organization should have some method for routinely advising employees about security issues. An excellent way to do that is to have an intranet site with bulletins posted to it. It is also a good idea to hold periodic training sessions for employees. These need not be lengthy or in depth. Most nontechnical employees only need an introduction to security concepts.
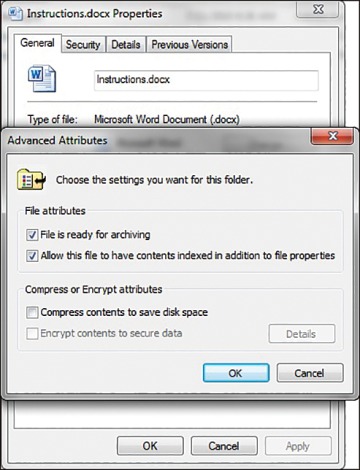
Figure 7.6 Windows EFS.
Unfortunately, taking these simple measures will not make you totally immune to corporate espionage. However, using these strategies will make any such attempts much more difficult for any perpetrator; thus, you will improve your organization’s data security.
