- Data Loss Prevention
- Data Loss Detection
- Data Classification, Labeling, and Tagging
- Obfuscation
- Anonymization
- Encrypted vs. Unencrypted
- Data Life Cycle
- Data Inventory and Mapping
- Data Integrity Management
- Data Storage, Backup, and Recovery
- Exam Preparation Tasks
- Review All Key Topics
- Define Key Terms
- Review Questions
Data Storage, Backup, and Recovery
While protecting data on a device is always a good idea, in many cases an organization must comply with an external standard regarding the minimum protection provided to the data on the storage device. For example, the Payment Card Industry Data Security Standard (PCI DSS) enumerates requirements that payment card industry players should meet to secure and monitor their networks, protect cardholder data, manage vulnerabilities, implement strong access controls, and maintain security policies.
The operations team also must determine which data is backed up, how often the data is backed up, and the method of backup used. An organization must determine how data is stored, including data in use and data that is backed up. While data owners are responsible for determining data access rules, data life cycle, and data usage, they must also ensure that data is backed up and stored in alternate locations to ensure that it can be restored.
Let’s look at an example. Suppose that an organization’s security administrator has received a subpoena for the release of all the email received and sent by the company’s chief executive officer (CEO) for the past three years. If the security administrator is only able to find one year’s worth of email records on the server, he should check the organization’s backup logs and archives before responding to the request. Failure to produce all the requested data could possibly have legal implications. The security administrator should restore the CEO’s email from an email server backup and provide whatever is available for up to the past three years from the subpoena date. Keep in mind, however, that the organization should provide all the data that it has regarding the CEO’s emails. If the security administrator is able to recover the past five years’ worth of the CEO’s email, the security administrator should notify the appropriate authorities and give them access to all five years’ data.
As a rule of thumb, in a subpoena situation, you should always provide all the available data, regardless of whether it exceeds the requested amount or any internal data retention policies. For example, if users are not to exceed 500 MB of storage but you find that a user has more than 3 GB of data, you should provide all that data in response to any legal requests. Otherwise, you and the organization could be held responsible for withholding evidence.
To design an appropriate data recovery solution, security professionals must understand the different types of data backups that can occur and how these backups are used together to restore the live environments.
Security professionals must understand the following data backup types and schemes:
■ Full backup
■ Differential backup
■ Incremental backup
■ Copy backup
■ Daily backup
■ Transaction log backup
■ First-in, first-out rotation scheme
■ Grandfather/father/son rotation scheme
The three main data backup types are full backups, differential backups, and incremental backups. To understand these three data backup types, you must understand the concept of archive bits. When a file is created or updated, the archive bit for the file is enabled. If the archive bit is cleared, the file will not be archived during the next backup. If the archive bit is enabled, the file will be archived during the next backup.
With a full backup, all data is backed up. During the full backup process, the archive bit for each file is cleared. A full backup takes the longest time and the most space to complete. However, if an organization uses only full backups, then only the latest full backup needs to be restored. Any backup that uses a differential or incremental backup will first start with a full backup as its baseline. A full backup is the most appropriate for offsite archiving.
In a differential backup, all files that have been changed since the last full backup will be backed up. During the differential backup process, the archive bit for each file is not cleared. A differential backup might vary from taking a short time and a small amount of space to growing in both the backup time and amount of space needed over time. Each differential backup will back up all the files in the previous differential backup if a full backup has not occurred since that time. In an organization that uses a full/differential scheme, the full backup and only the most recent differential backup must be restored, meaning only two backups are needed.
An incremental backup backs up all files that have been changed since the last full or incremental backup. During the incremental backup process, the archive bit for each file is cleared. An incremental backup usually takes the least amount of time and space to complete. In an organization that uses a full/incremental scheme, the full backup and each subsequent incremental backup must be restored. The incremental backups must be restored in order. If your organization completes a full backup on Sunday and an incremental backup daily Monday through Saturday, up to seven backups could be needed to restore the data. Table 4-2 provides a comparison of the three main backup types.
Table 4-2 Backup Types Comparison
Type |
Data Backed Up |
Backup Time |
Restore Time |
Storage Space |
|---|---|---|---|---|
Full backup |
All data |
Slowest |
Fast |
High |
Incremental backup |
Only new/modified files/folders since the last full or incremental backup |
Fast |
Moderate |
Lowest |
Differential backup |
All data since the last full backup |
Moderate |
Fast |
Moderate |
Copy and daily backups are two special backup types that are not considered part of any regularly scheduled backup scheme because they do not require any other backup type for restoration. Copy backups are similar to normal backups but do not reset the file’s archive bit. Daily backups use a file’s timestamp to determine whether it needs to be archived. Daily backups are popular in mission-critical environments where multiple daily backups are required because files are updated constantly.
Transaction log backups are used only in environments where it is important to capture all transactions that have occurred since the last backup. Transaction log backups help organizations recover to a particular point in time and are most commonly used in database environments.
Although magnetic tape drives are still in use today to back up data, many organizations today back up their data to optical discs, including CD-ROMs, DVDs, and Blu-ray discs; high-capacity, high-speed magnetic drives; solid-state drives; or other media. No matter the media used, retaining backups both onsite and offsite is important. Store onsite backup copies in a waterproof, heat-resistant, fire-resistant safe or vault.
As part of any backup plan, an organization should also consider the backup rotation scheme that it will use. Cost considerations and storage considerations often dictate that backup media be reused after a period of time. If this reuse is not planned in advance, media can become unreliable due to overuse. Two of the most popular backup rotation schemes are first-in, first-out and grandfather/father/son:
■ First-in, first-out (FIFO): In this scheme, the newest backup is saved to the oldest media. Although this is the simplest rotation scheme, it does not protect against data errors. If an error exists in the data, the organization might not have a version of the data that does not contain the error.
■ Grandfather/father/son (GFS): In this scheme, three sets of backups are defined. Most often these three definitions are daily, weekly, and monthly. The daily backups are the sons, the weekly backups are the fathers, and the monthly backups are the grandfathers. Each week, one son advances to the father set. Each month, one father advances to the grandfather set. Figure 4-3 displays a typical five-day GFS rotation using 21 tapes. The daily tapes are usually differential or incremental backups. The weekly and monthly tapes must be full backups.
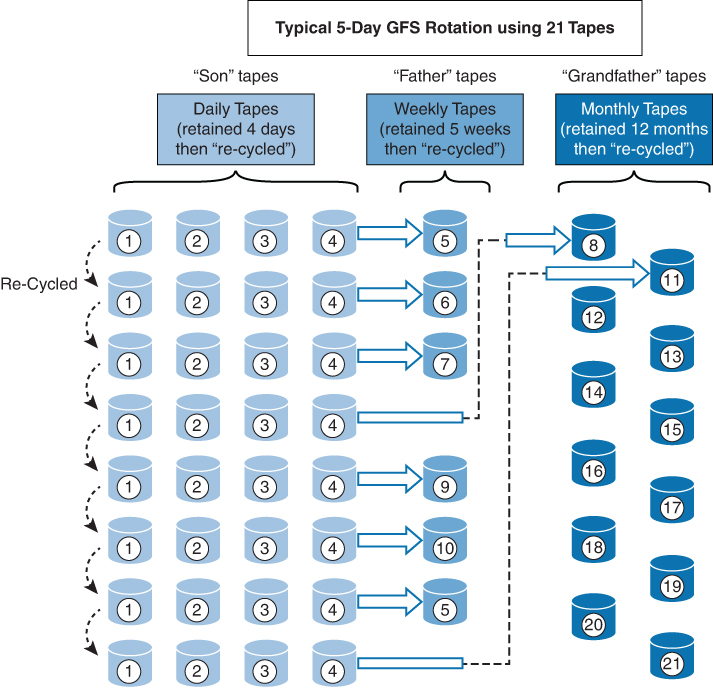
Figure 4-3 Grandfather/Father/Son Backup Rotation Scheme
Electronic backup solutions back up data more quickly and accurately than the normal data backups and are best implemented when information changes often. You should be familiar with the following electronic backup terms and solutions:
■ Electronic vaulting: This method involves copying files as modifications occur in real time.
■ Remote journaling: This method involves copying the journal or transaction log offsite on a regular schedule, in batches.
■ Tape vaulting: This method involves creating backups over a direct communication line on a backup system at an offsite facility.
■ Hierarchical storage management (HSM): This method involves storing frequently accessed data on faster media and less frequently accessed data on slower media.
■ Optical jukebox: This method involves storing data on optical discs and uses robotics to load and unload the optical discs as needed. This method is ideal when 24/7 availability is required.
■ Replication: This method involves copying data from one storage location to another. Synchronous replication uses constant data updates to ensure that the locations are close to the same, whereas asynchronous replication delays updates to a predefined schedule.
■ Cloud backup: Another method growing in popularity is to back up data to a cloud location.
Redundant Array of Inexpensive Disks (RAID)
RAID is a hard drive technology in which data is written across multiple disks in such a way that a disk can fail, and the data can be made available quickly by remaking disks in the array without resorting to a backup tape. The most common types of RAID are:
■ RAID 0: Also called disk striping, this method writes the data across multiple drives. While it improves performance, it does not provide fault tolerance. RAID 0 is depicted in Figure 4-4.
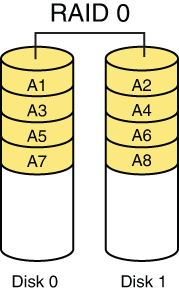
Figure 4-4 RAID 0
■ RAID 1: Also called disk mirroring, RAID 1 uses two disks and writes a copy of the data to both disks, providing fault tolerance in the event of a single drive failure. RAID 1 is depicted in Figure 4-5.
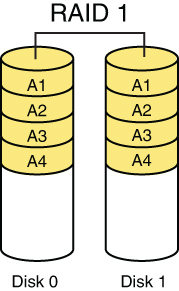
Figure 4-5 RAID 1
■ RAID 3: This method, which requires at least three drives, writes the data across all drives, as with striping, and then writes parity information to a single dedicated drive. The parity information is used to regenerate the data in the event of a single drive failure. The downfall of this method is that the parity drive is a single point of failure. RAID 3 is depicted in Figure 4-6.
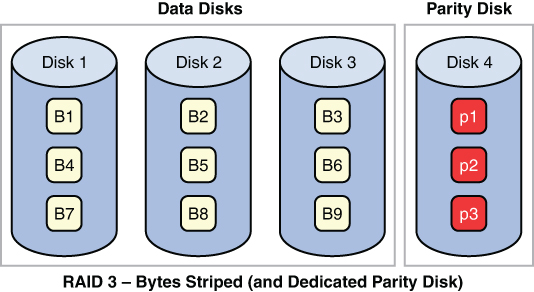
Figure 4-6 RAID 3
■ RAID 5: This method, which requires at least three drives, writes the data across all drives, as with striping, and then writes parity information across all drives as well. The parity information is used in the same way as in RAID 3, but it is not stored on a single drive, so there is no single point of failure for the parity data. With hardware RAID 5, the spare drives that replace the failed drives are usually hot swappable, meaning they can be replaced on the server while it is running. RAID 5 is depicted in Figure 4-7.
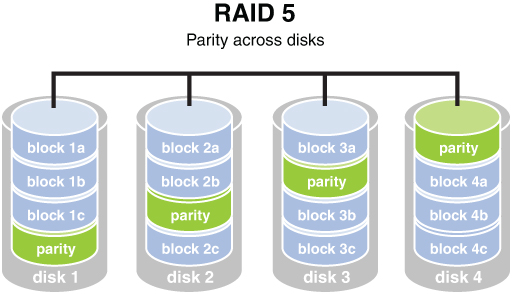
Figure 4-7 RAID 5
■ RAID 7: While not a standard but a proprietary implementation, this system incorporates the same principles as RAID 5 but enables the drive array to continue to operate if any disk or any path to any disk fails. The multiple disks in the array operate as a single virtual disk.
■ RAID 10: This method combines RAID 1 and RAID 0 and requires a minimum of four disks. However, most implementations of RAID 10 have four or more drives. A RAID 10 deployment contains a striped disk that is mirrored on a separate striped disk. Figure 4-8 depicts RAID 10.
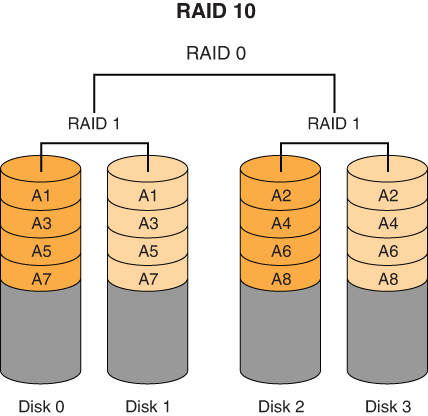
Figure 4-8 RAID 10
RAID can be implemented with software or with hardware, and certain types of RAID are faster when implemented with hardware. Both RAID 3 and 5 are examples of RAID types that are faster when implemented with hardware. Simple striping and mirroring (RAID 0 and 1), however, tend to perform well in software because they do not use the hardware-level parity drives. When software RAID is used, it is a function of the operating system. Table 4-3 summarizes the RAID types.
Table 4-3 RAID Types
RAID Level |
Minimum Number of Drives |
Description |
Strengths |
Weaknesses |
|---|---|---|---|---|
RAID 0 |
2 |
Data striping without redundancy |
Highest performance |
No data protection; if one drive fails, all data is lost |
RAID 1 |
2 |
Disk mirroring |
Very high performance; very high data protection; very minimal penalty on write performance |
High redundancy cost overhead; because all data is duplicated, twice the storage capacity is required |
RAID 3 |
3 |
Byte-level data striping with a dedicated parity drive |
Excellent performance for large, sequential data requests |
Not well suited for transaction-oriented network applications; the single parity drive does not support multiple, simultaneous read and write requests |
RAID 5 |
3 |
Block-level data striping with distributed parity |
Best cost/performance for transaction-oriented networks; very high performance and very high data protection; supports multiple simultaneous reads and writes; can also be optimized for large, sequential requests |
Write performance is slower than with RAID 0 or RAID 1 |
RAID 10 |
4 |
Disk striping with mirroring |
High data protection, which increases each time you add a new striped/mirror set |
High redundancy cost overhead; because all data is duplicated, twice the storage capacity is required |
