Securing the Enterprise Architecture by Implementing Data Security Techniques
- Data Loss Prevention
- Data Loss Detection
- Data Classification, Labeling, and Tagging
- Obfuscation
- Anonymization
- Encrypted vs. Unencrypted
- Data Life Cycle
- Data Inventory and Mapping
- Data Integrity Management
- Data Storage, Backup, and Recovery
- Exam Preparation Tasks
- Review All Key Topics
- Define Key Terms
- Review Questions
This sample chapter from CompTIA Advanced Security Practitioner (CASP+) CAS-004 Cert Guide covers CAS-004 Objective 1.4: Given a scenario, implement data security techniques for securing enterprise architecture.
This chapter covers the following topics:
■ Data Loss Prevention: This section covers blocking the use of external media, print blocking, Remote Desktop Protocol (RDP) blocking, clipboard privacy controls, restricted virtual desktop infrastructure (VDI) implementation, and data classification blocking.
■ Data Loss Detection: Topics covered include watermarking, digital rights management (DRM), network traffic decryption/deep packet inspection, and network traffic analysis.
■ Data Classification, Labeling, and Tagging: This section covers the handling of metadata and attributes.
■ Obfuscation: Topics covered include tokenization, scrubbing, and masking.
■ Anonymization: This section discusses the removal of personal information from data.
■ Encrypted vs. Unencrypted: This section discusses the impact of encryption.
■ Data Life Cycle: This section covers the stages of the data life cycle: creating, using, sharing, storing, archiving, and destroying.
■ Data Inventory and Mapping: This section discusses the importance of inventory and mapping.
■ Data Integrity Management: This section discusses issues with data changes and corruptions.
■ Data Storage, Backup, and Recovery: This section covers the use of redundant array of inexpensive disks (RAID).
This chapter covers CAS-004 Objective 1.4: Given a scenario, implement data security techniques for securing enterprise architecture.
Securing the enterprise architecture entails the use of many techniques and processes. In this chapter you’ll learn about data security techniques and how they can be used to support securing of the overall architecture.
Data Loss Prevention
As you learned in Chapter 1, preventing the loss of critical and sensitive data requires the use of both policies and procedures that reflect best practices and software tools such as data loss prevention (DLP) software to prevent malicious as well as inadvertent data leaks. In this opening section of the chapter you’ll learn about other techniques to prevent data loss.
Blocking Use of External Media
One of the many ways malware and other problems can be introduced to a network (right around all your fancy firewalls and security devices) is through the peripheral devices that users bring in and connect to their computers. Moreover, sensitive data can also leave your network this way. To address this, you should implement controls over the types of peripherals users can bring and connect (if any). The following sections look at the biggest culprits.
The use of any types of USB devices (thumb drives, external hard drives, network interfaces, and so on) should be strictly controlled—and in some cases prohibited altogether. Granular control of this issue is possible thanks to Windows Group Policy.
Some organizations choose to allow certain types of USB storage devices but require that the devices be encrypted before they can be used. It is also possible to allow some but not all users to use these devices, and it is even possible to combine digital rights management features with the policy to prohibit certain types of information from being copied to these devices.
For example, with Group Policy in Windows, you can use a number of policies to control the use of USB devices. Figure 4-1 shows a default domain policy to disallow the use of all removable storage. As you see, there are many other less drastic settings as well.
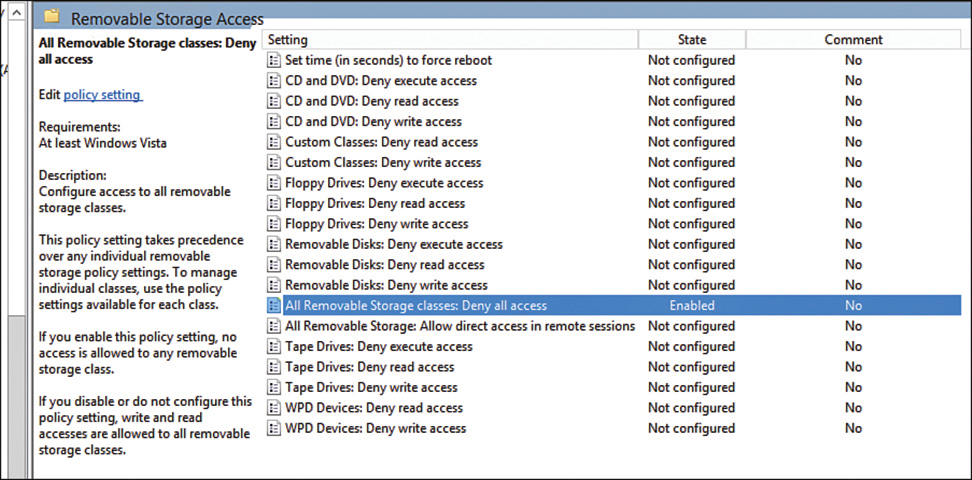
Figure 4-1 Controlling the Use of USB Devices
Print Blocking
As you learned in Chapter 1, blocking the printing of sensitive documents is entirely within the capabilities of DLP software. Print blocking can prevent someone from getting a copy of sensitive information off the printer and can prevent that information from being stored for any length of time in the memory of the print device, where it might be obtained by someone hacking into the printer.
Remote Desktop Protocol (RDP) Blocking
Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft that provides a graphical interface to connect to another computer over a network connection. Unlike Telnet and SSH, which allow only working from the command line, RDP enables you to work on a remote computer as if you were actually sitting at its console.
RDP sessions use native RDP encryption but do not authenticate the session host server. To mitigate this, you can use SSL/TLS for server authentication and to encrypt RDP session host server communications. This requires a certificate. You can use an existing certificate or the default self-signed certificate.
While RDP can be used for remote connections to a machine, it can also be used to connect users to a virtual desktop infrastructure (VDI). A VDI allows a user to connect from anywhere and work from a virtual desktop. Each user may have his or her own virtual machine (VM) image, or many users may use images based on the same VM.
The advantages and disadvantages of RDP are described in Table 4-1.
Table 4-1 Advantages and Disadvantages of RDP
Advantages |
Disadvantages |
|---|---|
Data is kept in the data center, so disaster recovery is easier. |
Sever downtime can cause issues for many users. |
Users can work from anywhere when using RDP in a VDI. |
Network issues can cause problems for many users. |
There is a potential reduction in the cost of business software when using an RDP model where all users are using the same base VM. |
Insufficient processing power in the host system can cause bottlenecks. |
Implementing and supporting RDP requires solid knowledge. |
RDP can be blocked at the firewall and at the system level by blocking port 3389.
Clipboard Privacy Controls
The clipboard function in desktops, laptops, and mobile devices is a convenient feature that stores information in memory until you paste it somewhere. But did you ever think of what happens after that? The information stays there until you copy over it! Moreover, in many systems, including Android, it has been found that any application can read that data without your permission.
While there is a fix to the Android issue, the point to be made is that organizations should be aware of this issue and take whatever steps are required to solve it as it may exist in your operating systems.
Restricted Virtual Desktop Infrastructure (VDI) Implementation
Virtual desktop infrastructures (VDIs) host desktop operating systems within a virtual environment in a centralized server. Users access the desktops and run them from the server. There are three models for implementing VDI:
■ Centralized model: All desktop instances are stored in a single server, which requires significant processing power on the server.
■ Hosted model: Desktops are maintained by a service provider. This model eliminates capital cost and is instead subject to operational cost.
■ Remote virtual desktops model: An image is copied to the local machine, which means a constant network connection is unnecessary.
Figure 4-2 compares the remote virtual desktop models (also called streaming) with centralized VDI.
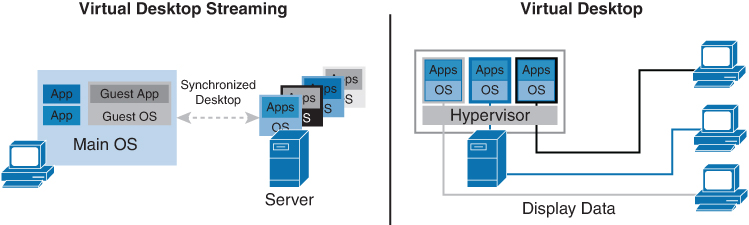
Figure 4-2 VDI Streaming and Centralized VDI
While a VDI environment can be beneficial, there are some steps that can be taken to restrict the infrastructure for security reasons:
■ Consider disallowing copy and paste functions.
■ Create an allow list (formerly known as a whitelist) or a block list (formerly known as a blacklist) to prevent users from accessing certain external sites or email providers.
■ Evaluate the primary image for unnecessary services.
■ Implement firewalls and antivirus software.
■ Require multifactor authentication.
Data Classification Blocking
Data should be classified based on its value to the organization and its sensitivity to disclosure. Assigning a value to data allows an organization to determine the resources that should be used to protect the data. Resources that are used to protect data include human resources, monetary resources, and access control resources. Classifying data as it relates to confidentiality, integrity, and availability (CIA) allows you to apply different protective measures.
After data is classified, the data can be segmented based on the level of protection it needs. Classification levels ensure that data is handled and protected in the most cost-effective manner possible. An organization should determine the classification levels it uses based on the needs of the organization. A number of commercial business and military and government information classifications are commonly used.
The information life cycle should also be based on the classification of the data. Organizations are required to retain certain information, particularly financial data, based on local, state, and federal laws and regulations.
Once data classification has occurred, you can then use the classifications to restrict access to data based on its classification. In Chapter 5, you’ll will learn about an access control system called mandatory access control (MAC) that uses such classification labels to block access to data.
