- "Do I Know This Already?" Quiz
- The Shared Responsibility Model
- Security Policies in AWS
- Access Controls
- Review All Key Topics
- Define Key Terms
- Q and A
The Shared Responsibility Model
The AWS Shared Responsibility Model is very simple. It divides the security responsibilities between two parties—the AWS customer (you) and Amazon (AWS). The fact that you are no longer responsible for a massive portion of the security required for scalable data centers is a huge advantage. You can leverage the massive budgets of Amazon and their intense expertise.
The next two sections of this chapter provide many examples of responsibilities in each part of the model. But for now, realize the Amazon responsibilities include the host operating system and virtualization layer down. From there, Amazon is also responsible for the physical security of the facilities in which the service operates. It is your (the customer’s) responsibility to secure the guest operating system (including updates and security patches), application software, and the AWS network security group firewall. Be aware that the client responsibilities will vary depending on which services the client chooses to use. The client responsibilities further vary based on the level of integration of AWS services consumed and their IT infrastructure. Laws and regulations that must be followed will also vary.
As shown in Figure 5-1, AWS is considered “Security of the Cloud”, and the customer’s responsibility is considered “Security in the Cloud.”
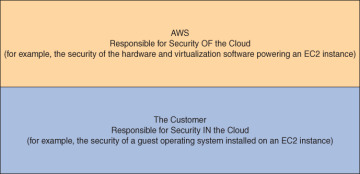
FIGURE 5-1 The AWS Shared Responsibility Model
In addition to partitioning the operational security concerns between the AWS client and AWS themselves, the Shared Responsibility Model applies to IT controls that are in use. Amazon categorizes these controls into three categories:
Inherited controls: These are security controls that the customer fully inherits from AWS. Perfect examples are the physical and environmental security controls used by Amazon.
Shared controls: These refer to controls that apply to both the infrastructure layer of Amazon and the customer responsibilities. Note that these shared controls apply to each domain in completely separate contexts or perspectives. For example, AWS provides the requirements (through controls) for the infrastructure. Then clients provide their own control implementation within their use of the services. Consider Identity and Access Management (IAM). The IAM service must be secured, meet regulatory compliance, and function as intended, while the customer should create well-crafted policies.
Customer-specific controls: These are security controls that the customer is solely responsible for. This varies based on the services they selected, of course. A great example would be when you apply specific patches to one of your operating systems on an EC2 instance.
Amazon Responsibilities
Remember, Amazon is considered responsible for security of the cloud. This means that AWS is responsible for protecting the infrastructure that runs the services that customers select. This encompasses the hardware and software required to power the AWS service, including the networking and facilities used.
Specific Amazon responsibilities would include the following:
Cloud software, including compute, storage, networking, and database software
Hardware
AWS Global Infrastructure (Regions, Availability Zones, Edge Locations)
Client Responsibilities
Remember, we consider the client responsible for security in the cloud. The specific services selected will cause variations in the client responsibilities. For example, if you are relying heavily on S3 for storage, you will be responsible for knowledge and proper configuration of the security permissions for your resources. Another example would be if the client chooses to use EC2 and run an operating system like Windows Server 2016. The client will be required to keep the operating system updated and patched. The client is also responsible for the application software required on this guest operating system. In addition, the client is responsible for the appropriate security group configuration for the EC2 instance.
Specific examples of client responsibilities would include the following:
Customer data
Platform, applications, Identity and Access Management (IAM)
Guest operating systems
Network and firewall configurations
Client-side data encryption
Server-side encryption (file system and or data)
Networking traffic protection (encryption, integrity, and identity)
Figure 5-2 shows an example of a customer checking the security groups settings that would apply to an EC2 instance. This is a perfect example of client responsibilities. AWS is responsible for making sure the security group functions as intended, but it is the client’s responsibility to configure it correctly.
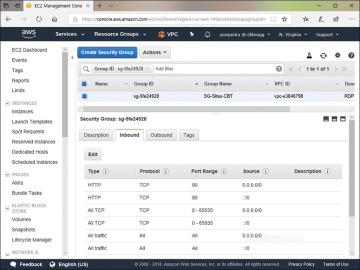
FIGURE 5-2 Checking the Security Groups Settings for an EC2 Instance
