- “Do I Know This Already?” Quiz
- Common Cloud Models
- Client-Side Virtualization Overview
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Client-Side Virtualization Overview
220-1101: Objective 4.2: Summarize aspects of client-side virtualization.

Microsoft (Hyper-V) and third-party vendors, such as Oracle (VirtualBox), VMware (VMware Workstation, VMware Fusion), and Parallels (Parallels Desktop), have offered virtualization solutions for some time. Virtualization enables a single computer to run two or more operating systems at the same time, using the same hardware resources.
To understand virtualization, make sure you understand these terms:
Virtual machine manager (VMM): A VMM, also called the hypervisor, is software that creates and manages virtual machines. It is a specialized operating system that uses minimal hardware resources so that memory and processing are available for the VMs it creates. (Later in this section, you see the differences between a VMM and a hypervisor.)
Virtual machine (VM): A VM is a machine created by a hypervisor/VMM that runs like any other computer. It usually needs an operating system installed on it to become functional. A VM uses the VMM/hypervisor for access to memory, CPU, network, video, and other resources.
Emulation: Emulation involves software-based reproduction of various operating systems, but without the functionality and resource use of virtualization.
When creating a VM, a VMM/hypervisor sets aside memory space that provides access to virtualized storage, ports, video, and other hardware, as well as a hard disk image file known as a virtual hard disk (VHD and the newer VHDX). When the VM is created, the user specifies the type of operating system that will be installed.
After the VM starts, the user can install the operating system from an .iso image file or from physical media. After the operating system is installed, the VM detects and uses the virtualized hardware that the VMM set up.
The VMM/hypervisor can start and stop the VM and modify the virtual hardware that the VM has access to. For example, the VMM can adjust the amount of RAM that the VM uses, change the virtual network adapter that the VM uses, and specify what type of network access the VM has. If a VM malfunctions, it can be stopped and restarted without affecting the host device.
A computer can run a different operating system in two ways:
Virtualization: In virtualization, the physical resources (for example, RAM, disk space, and CPU cycles) are divided between VMs that can run independently of each other. An operating system is loaded into each VM.
Emulation: In emulation, a full reproduction of a different operating system and different hardware is created by an emulation app, which is then used to run software made for that operating system. Some switch and router emulators have been created to provide training and testing without requiring expensive physical equipment. Other emulators have been created to enable modern PCs to run legacy video games created for systems such as the Atari 2600.
Several categories of virtualization exist: host/guest, hypervisor, server-hosted, and client-side virtualization.
Host/Guest Virtualization
In host/guest virtualization, a PC or workstation runs a standard operating system and a VMM that runs inside the host operating system; each VM is a guest operating system. Connections to hardware (networking, display, printing, and so on) are passed from the guest operating system, to the virtualization program, to the host computer’s operating system.
Figure 4-4 illustrates Oracle VM VirtualBox, a popular free host virtualizer. Other examples include Windows Virtual PC from Microsoft (for Windows 7), Microsoft Hyper-V (for Windows 8 and later), and VMware Workstation Player.
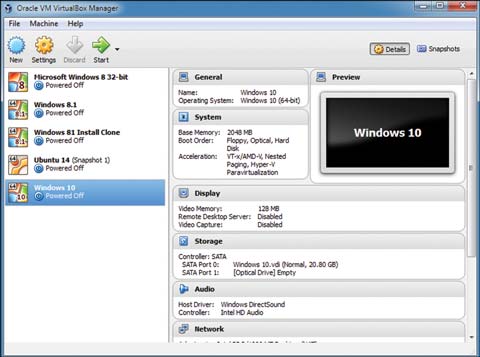
Figure 4.4 Oracle VM VirtualBox Manager Preparing to Start a VM
This type of virtualization is often used for client-side virtualization. However, client-side virtualization can also be centrally managed from the standpoint of the creation and management of VM images, although the images are being run locally.
Purpose of Virtual Machines
Software developers use virtual machines to develop applications and operating system enhancements. Three key ways developers use VMs are for sandboxing, test development, and application virtualization.
A common use for VMs is sandboxing, creating an isolated machine (or network of machines) where experiments can be run or software can be securely tested without risk to machines on the production network. For example, building and testing a new web server in a sandbox can be helpful so that mistakes happen before customers experience them.
The term sandboxing refers to a play area where children freely play with toys and sand inside a safe environment. Sandboxing is also a great way for students to learn new networking skills and try new code in an isolated, nonproduction environment where mistakes won’t result in expensive consequences.
Test development with virtual machines enables software developers to write and test computer applications. A key step in software development is seeing how code presents itself on a computer. This can involve trying several different scenarios, troubleshooting bugs that arise, and then tweaking the code. With virtual machines, a developer can capture different stages of development in snapshots and then try different tests and tasks to check performance. If the new code doesn’t work, they can easily revert to the last snapshot and try something else. Developers can also keep a library of different operating systems in one place, to test performance in different environments.
Application virtualization is the logical next step from hardware virtualization. Instead of installing applications on office computers, for example, users can install a desktop client that can access and manage application streaming from a company server located in a data center or in the cloud. The desktop client isolates the use of the streaming application from the user’s computer and any other applications in use. Basically, application virtualization allows users to access remote applications and use them as if they were installed on their own machine. This makes it easy to manage and maintain applications across an organization and enables different kinds of devices to access the applications, regardless of the device’s operating system or storage space.
Cross-platform virtualization is a type of application virtualization that can involve different underlying virtualization technologies. For example, the virtual software Microsoft 365 can be run across platforms as well as operating systems, so users on iPads, Linux devices, or macOS can have the same application software experience.
Legacy software and operating systems can be used in other types of application virtualization. Support specialists can run several legacy operating systems on one machine without rebooting their systems. These VMs are isolated, or containerized, so that they don’t interfere with other machines. Virtual machines even enable a single PC to run both 32-bit and 64-bit versions of the same operating system so that applications that run better in 32-bit mode can be run without the need for a separate computer. For example, in Figure 4-4, a 32-bit version of Windows 8 is virtualized but not currently running in the figure.
The virtual machines on a computer can perform different tasks at the same time, making it possible to do more work with less hardware investment.
Figure 4-5 illustrates the Microsoft Hyper-V Manager after creating a VM running Ubuntu Linux.
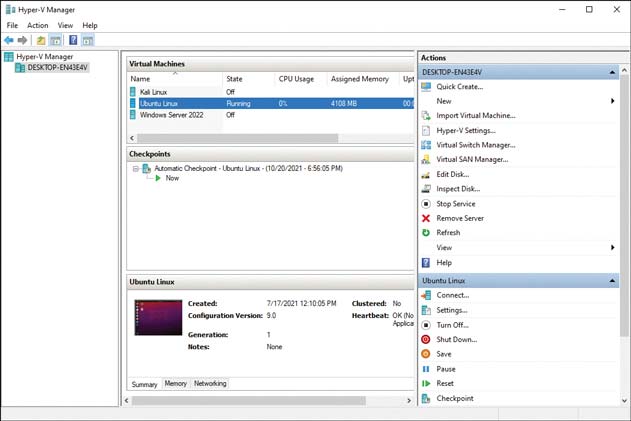
Figure 4.5 Hyper-V Manager Running Ubuntu Linux
By running virtual machines on servers, fewer physical servers are required to perform the same tasks, which leads to continuing cost savings, easier scaling to suit the workload, and easier disaster recovery.
System images can be centrally created, modified, and managed for easier installation. Because the VMM acts as a translator between the VM and the actual computer hardware, fewer problems arise from differences in system hardware.
Resource Requirements
A workstation that will be used for virtualization needs to be designed with fast multicore processors and as much RAM as possible, given the limitations of the motherboard and VMM (or host operating system). For this reason, the preferred approach is to use 64-bit processors and a 64-bit-compatible VMM (and host operating system, if hosted virtualization is being used instead of a hypervisor). The 64-bit operating systems or VMMs are not subject to the 4GB RAM limit imposed by 32-bit architecture.
Processors selected for a virtualization system should also feature hardware-assisted virtualization. The system BIOS/UEFI firmware must support this feature and be enabled in the system BIOS/UEFI firmware. Otherwise, VMs will run much more slowly, and some VMMs will not be supported.
If several VMs will be run at the same time on a workstation, using two or more displays is highly recommended.
Although a VM is created using an actual operating system instead of a reproduction of one, the physical hardware that will be used for the VMM must meet or exceed the minimum requirements for the VMM. Consider some examples:
VMware Workstation Player 16 is a simplified version of VMware. It requires a 1.3GHz or faster 64-bit processor, Intel CPU with VT-x support (enabled in BIOS/UEFI firmware) or AMD CPU with AMD-V support, and 2GB minimum (with 4GB or more recommended).
Hyper-V requires a 64-bit CPU with Data Execution Prevention (DEP) and hardware virtualization (enabled in BIOS/UEFI firmware), second-level address translation (SLAT), and a minimum of 4GB of RAM (with more recommended).
Security Requirements
Virtual networks require the same attention to security details as physical networks. Because a single physical computer can house two or more VMs, knowing which computers in an organization are using VMs is a vital first step in securing a virtualized environment. The following are some issues to consider:
Network traffic monitoring: When multiple VMs running on a single physical workstation or server communicate with each other, the hypervisor must monitor the traffic unless it is routed to the physical network and then back to the other VM. A feature known as extensible switch modules enables the operating system to monitor network traffic between VMs.
VMs backups: Virtualized storage needs to be backed up with tools made especially for VMs. A VM backup needs to include configuration files and virtual disks to ensure that the VM can be restored wherever needed. Most VMMs and hypervisors include a feature known as virtual machine checkpoints (or virtual machine snapshots). A checkpoint saves the state, data, and hardware configuration of a VM while it is running.
Updates and patches: Updates and patches must be kept current. Additionally, antivirus software must be installed and updated because the host machine cannot scan the VMs for viruses.
Security: A VMM that enables sandboxing (isolation) of each VM and that provides physical partitioning of resources provides better security against attacks.
Best security practices for VMMs and VMs: Operating systems and apps in VMs must be kept up-to-date and need to use firewalls and anti-malware to protect the VM. VMMs also need to be kept up-to-date, and remote administration should be secured by using a VPN. Connections between the VMs, such as clipboards or file sharing, should be limited to only those that are necessary.
