Bandwidth Management
While the main concern with routing is ensuring that data packets (as well as control plane packets) reach their rightful destinations, it is the job of quality of service (QoS) to ensure that packets do not suffer from long delays (latency) or, worse, dropped packets.
QoS is actually a suite of technologies that allows you to strategically optimize network performance for select traffic types. For example, in today’s converged networks (that is, networks simultaneously transporting voice, video, and data), some applications (for example, voice) might be more intolerant of delay (or latency) than other applications; for example, an FTP file transfer is less latency sensitive than a VoIP call. Fortunately, through the use of QoS technologies, you can identify which traffic types need to be sent first, how much bandwidth to allocate to various traffic types, which traffic types should be dropped first in the event of congestion, and how to make the most efficient use of the relatively limited bandwidth of an IP WAN. This section introduces QoS and a collection of QoS mechanisms.
Introduction to QoS
A lack of bandwidth is the overshadowing issue for most network quality problems. Specifically, when there is a lack of bandwidth, packets might suffer from one or more of the symptoms listed in Table 10-3.
Table 10-3 Three Categories of Quality Issues
Issue |
Description |
|---|---|
Delay |
Delay is the time required for a packet to travel from source to destination. You might have witnessed delay on the evening news when the news anchor is talking via satellite to a foreign news correspondent. Because of the satellite delay, the conversation begins to feel unnatural. |
Jitter |
Jitter is the uneven arrival of packets. For example, imagine a VoIP conversation where packet 1 arrives at a destination router. Then, 20 ms later, packet 2 arrives. After another 70 ms, packet 3 arrives, and then packet 4 arrives 20 ms behind packet 3. This variation in arrival times (that is, variable delay) is not due to dropped packets, but the jitter might be interpreted by the listener as dropped packets. |
Drops |
Packet drops occur when a link is congested and a router’s interface queue overflows. Some types of traffic, such as UDP traffic carrying voice packets, are not retransmitted if packets are dropped. |
Fortunately, QoS features available on many routers and switches can recognize important traffic and then treat that traffic in a special way. For example, you might want to allocate 128Kbps of bandwidth for your VoIP traffic and give that traffic priority treatment.
Consider water flowing through a series of pipes with varying diameters. The water’s flow rate through those pipes is limited to the water’s flow rate through the pipe with the smallest diameter. Similarly, as a packet travels from source to destination, its effective bandwidth is the bandwidth of the slowest link along that path. For example, in Figure 10-13, notice that the slowest link speed is 256Kbps. This weakest link becomes the effective bandwidth between client and server.
Because the primary challenge of QoS is a lack of bandwidth, the logical question is, “How do we increase available bandwidth?” A knee-jerk response to that question is often “Add more bandwidth.” However, more bandwidth often comes at a relatively high cost.
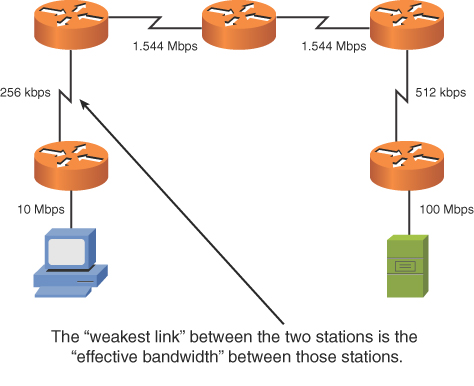
FIGURE 10-13 Effective Bandwidth of 256Kbps
Think of your network as a highway system in a large city. During rush hour, the lanes of the highway are congested; during other periods of the day, the lanes might be underutilized. Instead of just building more lanes to accommodate peak traffic rates, the highway engineers might add a carpool lane to give higher priority to cars with two or more occupants. Similarly, you can use QoS features to give your mission-critical applications higher-priority treatment in times of network congestion.
QoS Configuration Steps
The mission statement of QoS could read something like this: “To categorize traffic and apply a policy to those traffic categories, in accordance with a QoS policy.” Understanding this underlying purpose of QoS can help you better understand the three basic steps involved in QoS configuration:
Step 1. Determine network performance requirements for various traffic types. For example, consider these design recommendations for voice, video, and data traffic:
Voice: No more than 150 ms of one-way delay; no more than 30 ms of jitter; and no more than 1% packet loss.
Video: No more than 150 ms of one-way delay for interactive voice applications (for example, video conferencing); no more than 30 ms of jitter; and no more than 1% of packet loss.
Data: Applications have varying delay and loss requirements. Therefore, data applications should be categorized into predefined classes of traffic, where each class is configured with specific delay and loss characteristics.
Step 2. Categorize traffic into specific categories. For example, you might have a category named Low Delay for voice and video packets in that category. You might also have a Low Priority class for traffic such as music downloads from the Internet.
Step 3. Document your QoS policy and make it available to your users. Then, for example, if users complain that their network gaming applications are running slowly, you can point them to your corporate QoS policy, which describes how applications such as network gaming have best-effort treatment, while VoIP traffic receives priority treatment.
The actual implementation of these steps varies based on the specific device you are configuring. In some cases, you might be using the command-line interface (CLI) of a router or switch. In other cases, you might have some sort of graphical user interface (GUI) through which you configure QoS on your routers and switches.
QoS Components
QoS features are categorized into one of the three categories shown in Table 10-4.
Table 10-4 Three Categories of QoS Mechanisms
Issue |
Description |
|---|---|
Best effort |
Best-effort treatment of traffic does not truly provide QoS to that traffic because there is no reordering of packets. Best effort uses a first-in, first-out (FIFO) queuing strategy, where packets are emptied from a queue in the same order in which they entered the queue. |
Integrated Services (IntServ) |
IntServ is often referred to as hard QoS because it can make strict bandwidth reservations. IntServ uses signaling among network devices to provide bandwidth reservations. Resource Reservation Protocol (RSVP) is an example of an IntServ approach to QoS. Because IntServ must be configured on every router along a packet’s path, the main drawback of IntServ is its lack of scalability. |
Differentiated Services (DiffServ) |
DiffServ, as its name suggests, differentiates between multiple traffic flows. Specifically, packets are marked, and routers and switches can then make decisions (for example, dropping or forwarding decisions) based on those markings. Because DiffServ does not make an explicit reservation, it is often called soft QoS. Most modern QoS configurations are based on the DiffServ approach. |
Figure 10-14 summarizes these three QoS categories.
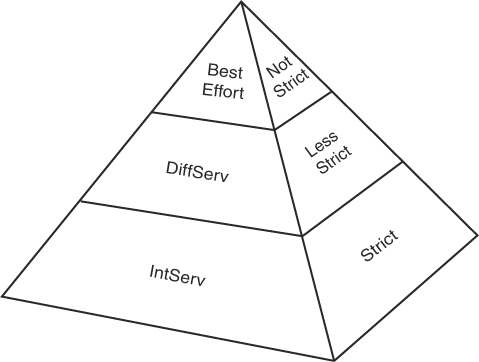
FIGURE 10-14 QoS Categories
QoS Mechanisms
As previously mentioned, a DiffServ approach to QoS marks traffic. However, for markings to impact the behavior of traffic, a QoS tool must reference those markings and alter the packets’ treatment based on them. The following is a collection of commonly used QoS mechanisms:
Classification
Marking
Congestion management
Congestion avoidance
Policing and shaping
Link efficiency
While all of these mechanisms can be considered important, this chapter focuses on the main bandwidth management tools policing and traffic shaping.
Policing and Traffic Shaping
Instead of making a minimum amount of bandwidth available for specific traffic types, you might want to limit available bandwidth. Both traffic policing and traffic shaping tools can accomplish this objective. Collectively, these tools are called traffic conditioners.
Policing can be used in either the inbound or the outbound direction, and it typically discards packets that exceed the configured rate limit, which you can think of as a speed limit for specific traffic types. Because policing drops packets, resulting in retransmissions, it is recommended for higher-speed interfaces.
Shaping buffers (and therefore delays) traffic exceeding a configured rate. Therefore, shaping is recommended for slower-speed interfaces.
Because traffic shaping (and policing) can limit the speed of packets exiting a router, a question arises: “How do you send traffic out of an interface at a rate that is less than the physical clock rate of the interface?” For this to be possible, shaping and policing tools do not transmit all the time. Specifically, they send a certain number of bits or bytes at line rate, and then they stop sending until a specific timing interval (for example, one-eighth of a second) is reached. After the timing interval is reached, the interface again sends a specific amount of traffic at the line rate. It stops and waits for the next timing interval to occur. This process continually repeats, allowing an interface to send an average bandwidth that might be below the physical speed of the interface. This average bandwidth is called the committed information rate (CIR). The number of bits (the unit of measure used with shaping tools) or bytes (the unit of measure used with policing tools) that is sent during a timing interval is called the committed burst (Bc). The timing interval is written as Tc.
For example, imagine that you have a physical line rate of 128Kbps, but the CIR is only 64Kbps. Also, assume that there are eight timing intervals in a second (that is, Tc = 1/8 second = 125 ms), and during each of those timing intervals, 8000 bits (the committed burst parameter) are sent at the line rate. Therefore, over the period of a second, 8000 bits are sent (at the line rate) eight times, for a grand total of 64,000 bits per second, which is the CIR. Figure 10-15 illustrates this shaping of traffic to 64Kbps on a line with a rate of 128Kbps.
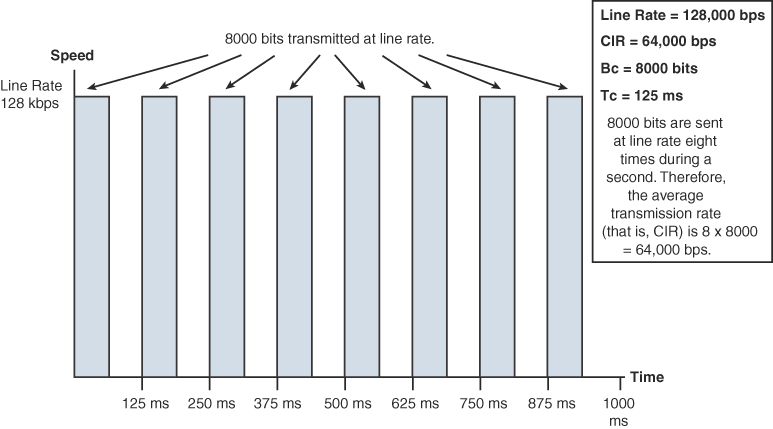
FIGURE 10-15 Traffic Shaping
If all the Bc bits (or bytes) are not sent during a timing interval, there is an option to bank those bits and use them during a future timing interval. The parameter that allows this storing of unused potential bandwidth is called the excess burst (Be) parameter. The Be parameter in a shaping configuration specifies the maximum number of bits or bytes that can be sent in excess of the Bc during a timing interval, if those bits are indeed available. For those bits or bytes to be available, they must have gone unused during previous timing intervals. Policing tools, however, use the Be parameter to specify the maximum number of bytes that can be sent during a timing interval. Therefore, in a policing configuration, if the Bc equals the Be, no excess bursting occurs. If excess bursting occurs, policing tools consider this excess traffic to be exceeding traffic. Policing tools consider traffic that conforms to (that is, does not exceed) a specified CIR to be conforming traffic.
The relationship between the Tc, Bc, and CIR is given with this formula: CIR = Bc / Tc. Alternatively, the formula can be written as Tc = Bc / CIR. Therefore, if you want a smaller timing interval, you can configure a smaller Bc.
