Routing Protocol Characteristics
Before examining the characteristics of routing protocols, we need to look at the important distinction between a routing protocol and a routed protocol:
A routing protocol (for example, RIP, OSPF, or EIGRP) is a protocol that advertises route information between routers.
A routed protocol is a protocol with an addressing scheme (for example, IP) that defines different network addresses. Traffic can then be routed between defined networks, perhaps with the assistance of a routing protocol.
This section looks at routing protocol characteristics, such as how believable a routing protocol is compared to other routing protocols. In addition, in the presence of multiple routes, different routing protocols use different metrics to determine the best path. A distinction is made between interior gateway protocols (IGPs) and exterior gateway protocols (EGPs). Finally, this section discusses different approaches to making route advertisements.
Believability of a Route
If a network is running more than one routing protocol (maybe as a result of a corporate merger), and a router receives two route advertisements from different routing protocols for the same network, which route advertisement does the router believe? Interestingly, some routing protocols are considered to be more believable that others. For example, a Cisco router would consider EIGRP to be more believable than RIP.
The index of believability is called administrative distance (AD). Table 10-1 shows the AD values for various sources of routing information. Note that lower AD values are more believable than higher AD values.
Table 10-1 Administrative Distance
Routing Information Source |
AD Value |
|---|---|
Directly connected network |
0 |
Statically configured network |
1 |
EIGRP |
90 |
OSPF |
110 |
RIP |
120 |
External EIGRP |
170 |
Unknown or unbelievable |
255 (considered to be unreachable) |
Metrics
Some networks might be reachable via more than one path. If a routing protocol knows of multiple paths to reach such a network, which route (or routes) does the routing protocol select? Actually, it varies depending on the routing protocol and what that routing protocol uses as a metric (that is, a value assigned to a route). Lower metrics are preferred over higher metrics.
Some routing protocols support load balancing across equal-cost paths; this is useful when a routing protocol knows of more than one route to reach a destination network and those routes have equal metrics. EIGRP can even be configured to do load balancing across unequal-cost paths.
Different routing protocols can use different parameters in their calculation of a metric. The specific parameters used for a variety of routing protocols are presented later in this chapter.
Interior Versus Exterior Gateway Protocols
Routing protocols can also be categorized based on the scope of their operation. Interior gateway protocols (IGPs) operate within an autonomous system, where an autonomous system is a network under a single administrative control. Conversely, exterior gateway protocols (EGPs) operate between autonomous systems.
Consider Figure 10-9. Routers R1 and R2 are in one autonomous system (AS 65002), and routers R3 and R4 are in another autonomous system (AS 65003). Within those autonomous systems, an IGP is used to exchange routing information. However, router ISP1 is a router in a separate autonomous system (AS 65001) that is run by a service provider. An EGP (typically, Border Gateway Protocol) is used to exchange routing information between the service provider’s autonomous system and each of the other autonomous systems.
Route Advertisement Method
Another characteristic of a routing protocol is how it receives, advertises, and stores routing information. The two fundamental approaches are distance vector and link state.
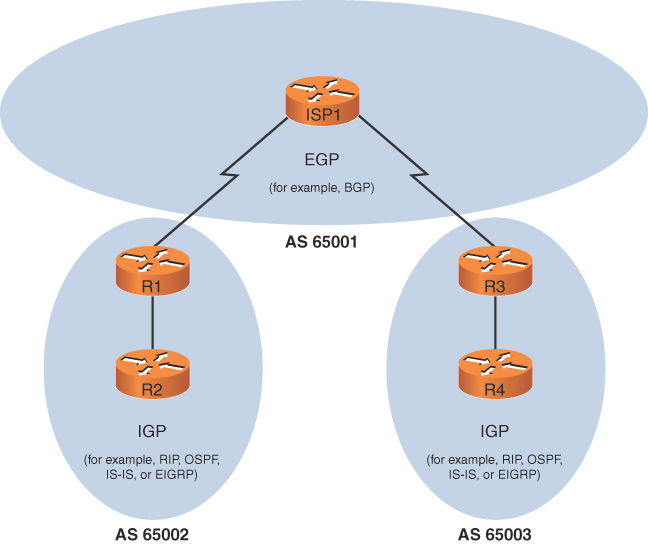
FIGURE 10-9 IGPs Versus EGPs
Distance Vector
A distance-vector routing protocol sends a full copy of its routing table to its directly attached neighbors. This is a periodic advertisement, meaning that even if there have been no topological changes, a distance-vector routing protocol will, at regular intervals, advertise again its full routing table to its neighbors.
Obviously, this periodic advertisement of redundant information is inefficient. Ideally, you want a full exchange of route information to occur only once and subsequent updates to be triggered by topological changes.
Another drawback to distance-vector routing protocols is the time they take to converge, which is the time required for all routers to update their routing tables in response to a topological change in a network. Hold-down timers can speed the convergence process. After a router makes a change to a route entry, a hold-down timer prevents any subsequent updates for a specified period of time. This approach helps stop flapping routes (which are routes that oscillate between being available and unavailable) from preventing convergence.
Yet another issue with distance-vector routing protocols is the potential of a routing loop. To illustrate, consider Figure 10-10. In this topology, the metric being used is hop count, which is the number of routers that must be crossed to reach a network. As one example, router R3’s routing table has a route entry for network 10.1.1.0/24 available off router R1. For router R3 to reach that network, two routers must be transited (routers R2 and R1). As a result, network 10.1.1.0/24 appears in router R3’s routing table with a metric (hop count) of 2.
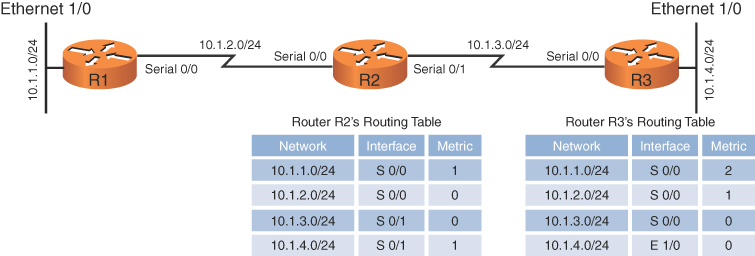
FIGURE 10-10 Routing Loop: Before Link Failure
Continuing with the example, imagine that interface Ethernet 1/0 on router R3 goes down. As shown in Figure 10-11, router R3 loses its directly connected route (with a metric of 0) to network 10.1.4.0/24. However, router R2 had a route to 10.1.4.0/24 in its routing table (with a metric of 1), and this route was advertised to router R3. Router R3 adds this entry for 10.1.4.0 to its routing table and increments the metric by 1.
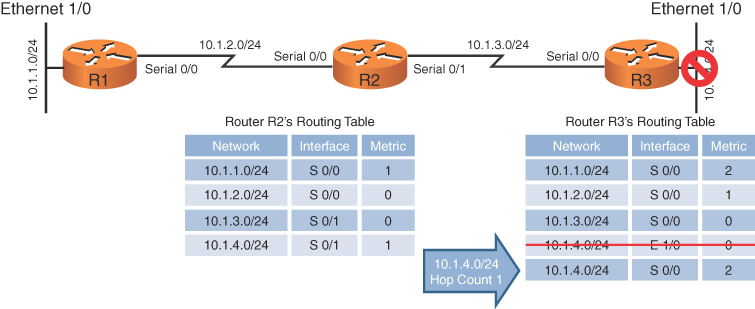
FIGURE 10-11 Routing Loop: After Link Failure
The problem with this scenario is that the 10.1.4.0/24 entry in router R2’s routing table was due to an advertisement router R2 received from router R3. Now, router R3 is relying on that route, which is no longer valid. The routing loop continues as router R3 advertises its newly learned route 10.1.4.0/24 with a metric of 2 to its neighbor, router R2. Because router R2 originally learned the 10.1.4.0/24 network from router R3, when it sees router R2 advertising that same route with a metric of 2, the network gets updated in router R2’s routing table to have a metric of 3, as shown in Figure 10-12.
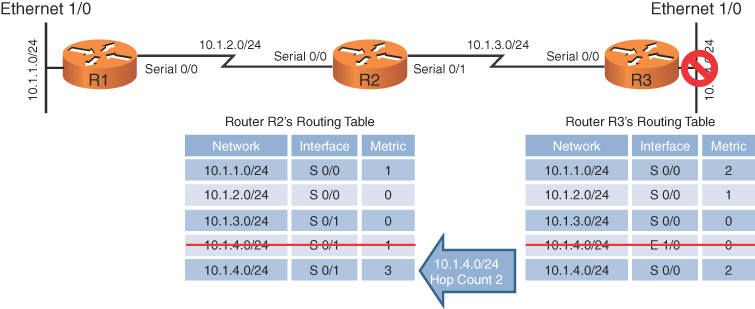
FIGURE 10-12 Routing Loop: Routers R2 and R3 Incrementing the Metric for 10.1.4.0/24
The metric for the 10.1.4.0/24 network continues to increment in the routing tables for both routers R2 and R3 until the metric reaches a value considered to be an unreachable value (for example, 16 in the case of RIP). This process is referred to as a routing loop.
Distance-vector routing protocols typically use one of two approaches for preventing routing loops:
Split horizon: The split-horizon feature prevents a route learned on one interface from being advertised back out that same interface.
Poison reverse: The poison-reverse feature causes a route received on one interface to be advertised back out that same interface with a metric that is considered to be infinite.
In the previous example, either approach would have prevented router R3 from adding the 10.1.4.0/24 network to its routing table based on an advertisement from router R2.
Link State
Rather than having neighboring routers exchange their full routing tables with one another, a link-state routing protocol allows routers to build a topological map of the network. Then, much like a Global Positioning System (GPS) device in a car, a router can execute an algorithm to calculate an optimal path (or paths) to a destination network.
Routers send link-state advertisements (LSAs) to advertise the networks they know how to reach. Routers then use those LSAs to construct the topological map of a network. The algorithm that runs against this topological map is Dijkstra’s shortest path first algorithm.
Unlike distance-vector routing protocols, link-state routing protocols exchange full routing information only when two routers initially form their adjacency. Then routing updates are sent in response to changes in the network, as opposed to being sent periodically. Also, link-state routing protocols benefit from shorter convergence times compared to distance-vector routing protocols.
