Dating Apps
There were 3.6 million applications (“apps”) on Google Play and 2.1 million iOS applications on Apple’s App Store in 2017, and a mere 8.5% of those apps were cross-platform, meaning that they were available for both iOS and Android. Adults in the United States are using mobile devices in ways that could not be imagined just 15 years ago. According to Pew Research Center’s report on mobile dating, 15% of adults (ages 18 and older), in the United States, have reported that they have used online dating sites or mobile dating apps. Dating site usage has nearly tripled for young adults (18 through 24) in just two years, from 10% to 27%. Therefore, it is important for investigators to understand the evidence available from mobile dating apps. Moreover, the prevalence of social engineering—using data derived from social media accounts—means that dating apps are a cause for concern in terms of organizational risk.
With the recent increase in online match-making connections, in a post-Snowden era where privacy has become a major concern, we might question whether dating applications are utilizing personal data ethically. In March 2018, a security flaw in the Grindr app disclosed user location data, which could have exposed app users to harassment; Grindr is a dating app, primarily used to connect gay men and unfortunately has facilitated numerous attacks against many gay men. Thus, understanding the available evidence from a dating app is extremely important because of the nature of the crimes being committed, the links to social media, the personal information available, and the location and communication capabilities of these apps.
Tinder
As of 2018, Tinder had 57 million users worldwide. Millions of Tinder subscribers pay for a premium service: Tinder Plus or Tinder Gold. Tinder is used in 190 countries and supports 40 languages. Owned by Match Group, Inc., Tinder is a location-based, social media, application for dating. The app connects singles and allows them to “Swipe Right”, if they wish to connect with another individual, or they can “Swipe Left”, if they are not interested. The user can also “Swipe Up” (called a “super like”), which notifies the user that they have been “Super Liked”. The ability to passively block communication with someone, whom a user is not interested in, is what makes Tinder appealing for so many people.
Tinder gives the user the ability to chat with individuals who have both swiped right pseudo-anonymously. A user is not required to divulge his cellphone number, and a user can make his own judgment about how much personal information he wishes to share with another user when matched. Chats within the application are stored chronologically and can be deleted.
Tinder also offers a Web-based version of their service at gotinder.com and tinder.com (see Figure 10.21). The website gives users the ability to use Tinder’s services without a smartphone. The user simply logs in with their credentials . However, location services must be turned on, in the browser application, to use the Web version of the application.
FIGURE 21.10 www.gotinder.com user profile
One of the most popular features of Tinder is the ability for users to synchronize their personal Instagram page with their Tinder profile (see Figure 10.22). This feature allows someone whom they have matched with (both parties swipe right) to have the ability to view the other user’s Instagram profile. This allows a user to visit a Tinder user’s Instagram profile, even if the Instagram account is set to private. Connecting social media accounts in this fashion is referred to as “deep-linking”.
FIGURE 22.10 Tinder app linked to Instagram
A Spotify account can also be synchronized with a Tinder account, using deep-linking. This feature allows the users to share their personal playlists with individuals that they have matched with. A user can apply an “Anthem” to their profile, which can be the user’s favorite song.
Using Robtex (robtex.com), we can quickly map out the domains associated with Tinder, some of which are displayed in Figure 10.23.

FIGURE 10.23 DNS data for gotinder.com (Source: Robtex.com)
Utilizing tools, like Robtex and traceroute, and whatismyipaddress.com, an investigator can determine where app user data is being stored and determining jurisdiction.
An analysis of Tinder’s DNS connections shows that the Tinder app connects a user’s profile with servers managed by Facebook, Leanplum, Appsflyer, DoubleClick, and many other companies. Using Debookee, it was possible to intercept Tinder messages, an example of which can be viewed in Figure 10.24. Figure 10.25 displays sample DNS connections associated with Tinder and captured with Debookee.
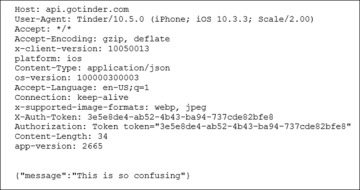
FIGURE 10.24 Debookee HTTPS packet capture and decrypted chat message
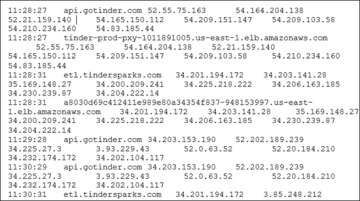
FIGURE 10.25 DNS sample traffic captured with Debookee
Using BlackLight, a static analysis of the user data, contained in the Tinder SQLite database on an iPhone, reveals that the data is stored in plaintext. Interestingly, a private Instagram account could be viewed during this analysis. Moreover, that (private) Instagram account stored Instagram photos from other users without that user’s consent. User chat sessions, usernames, and Instagram data were all stored in plaintext on the iPhone test device. A URL can be found associated with each profile, which enables the user to access another user’s profile page—even if it is marked private.
An examination of the Tinder SQLite database also revealed the location of other Tinder users in close proximity, as shown in Figure 10.26.
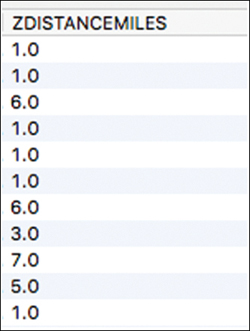
FIGURE 10.26 ZDISTANCEMILES displays the distances to other users
It is also possible to obtain more precise information about users’ locations in the vicinity, as shown in Figure 10.27.
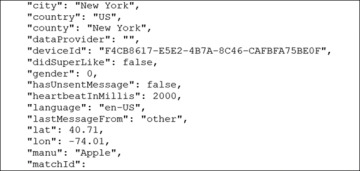
FIGURE 10.27 Location data from the Tinder app
Grindr
While there are many mobile apps that provide corroborating evidence in an investigation, Grindr is an app that has been used to perpetrate some of the most heinous crimes. Therefore, it is an app that warrants special attention for investigators. Stephen Port, from East London, U.K., was called the Grindr Serial Killer after he was charged with murdering four men that he met on Grindr. There are literally hundreds, if not thousands of cases, where Grindr has been used, by criminals, to lure victims and subsequently commit crimes, which include murder, assault, and robbery. The good news is that the Grindr app stores a wealth of information, in plaintext, which may help investigators and prosecutors.
Grindr was launched in 2009 and is the world’s leading social networking application for gay, bisexual, trans and queer people. Grindr, unlike traditional dating apps, like Tinder and Bumble, is designed to find individuals in close proximity to the user. The smallest value for distance that Tinder/Bumble incorporates into their platform is one mile but Grindr will literally go to “zero feet away”, and this is explicitly stated in the “About” section of their webpage. There is no “swipe left” or “dislike” and individuals are listed from closest to farthest away. There are no parameters to meet a certain type of user like with Tinder (age range, gender, etc.). If a user wants to engage with another user, they simply “Tap” that individual’s profile, and they will be notified. The other user is then notified that they have been tapped. At this point, both users can immediately send an unlimited number of messages, which can be texts, images, and “GayMoji” stickers.
Popular dating applications, like Tinder and Bumble, require both users to explicitly indicate their willingness to engage with the other. However, Grindr does not require mutual consent to begin a chat session. There is a safeguard to protect from harassment, where the user can simply delete the “Tap” from a user they do not like, ending the message session. There are different types of “Taps” that give a visual representation of what the individual is looking for. There is a “Hi” icon tap for if the individual just wants to introduce himself or herself, or perhaps just chat. There is a “flame” icon tap for if the individual is interested in dating or sex. And finally, there is a “smiling devil Emoji” icon tap if the individual is looking for a “no strings attached” interaction. If the message is a text, then it will be previewed next to the user’s profile. If it is a photo or video, it will have a small “Camera Icon” instead. A relatively new feature to the Grindr message function is “Read” receipts that will indicate whether the person a user messages has actually opened the message. Figure 10.28 shows the “Flame” tap and “Smiling Devil Tap” emojis.
Grindr has reached more than 196 countries with more than 3.6 million daily active users (2018). On average these users send 228 million messages and 20 million photos each day.
To date, there is no Web interface for Grindr, which supports user chat. However, the user can create a profile at www.grindr.com.
Grindr Evidence
Grindr does support deep-linking to social media services, which includes Facebook, Instagram, and Twitter. A feature of Grindr is the opportunity for a user to sync their personal Instagram page directly to their Grindr profile. This feature allows someone who has tapped on a user’s Grindr profile to directly view the user’s Instagram profile page. Grindr then gives the user the option to quickly switch directly to Instagram. This feature gives the user even more redundancy in deciding if the person they have matched with is someone they would still like to engage with. Both users still must go through the process of requesting to follow and allowing a follow through Instagram if the Instagram account is private. Like Instagram, a Facebook account can also be synced with a Grindr account, and it provides an easy one-click link directly to the Facebook profile on the Facebook app.
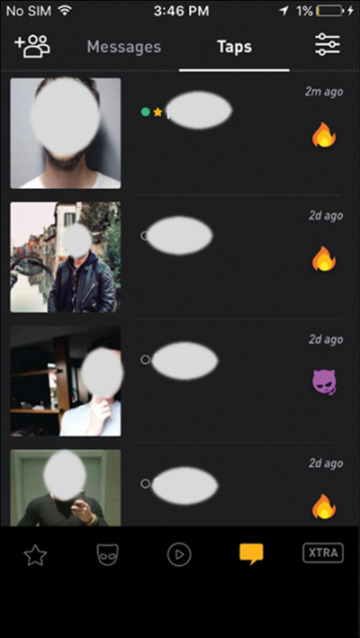
FIGURE 10.28 Grindr mobile user chat interface
Grindr appears to connect with a number of IP addresses, as displayed in Figure 10.29. A trace of these IP addresses goes back to San Francisco, California.
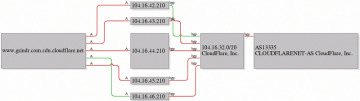
FIGURE 10.29 www.grindr.com.cdn.cloudfare.net DNS map (Source: Robtex.com)
Debookee could identify Grindr communication packets from iPhones, while they are being transmitted. The content is TLS/SSL encrypted. However, using the TLS decryption tool, offered by Debookee, it is possible to view a substantial amount of the DNS and HTTPS traffic, as shown in Figure 10.30. Messages are sent through cdns.grindr.com on port 443, using Amazon Web Services Inc. Although Grindr has made security updates to its platform since 2008, the third parties responsible for advertising, like Nexage, still pass sensitive PII, which includes exact location, sex, and age in plaintext, as shown in Figure 10.31. This means that anyone performing a man-in-the-middle attack could see that data.
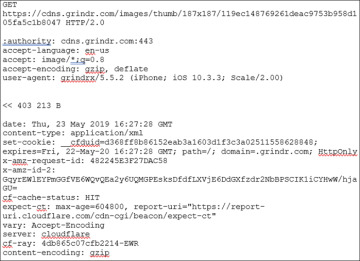
FIGURE 10.30 Debookee HTTPS packet capture decryption
In a SQLite database, named greventLog.sqlite, you can find multiple latitude/longitude references stored in plaintext, as shown in Figure 10.32. Each message transaction is sent with updated location data. A latitude/longitude converter can then be used to find the address.
Messages in Grindr are unencrypted and are stored in plaintext. After viewing the data, a user has a unique identifier that is displayed in the “from” portion and in the “to” portion, which is a unique ID for the subject’s iPhone, as shown in Figure 10.33. After combing through PersistenceStore.bin, it is possible to see all message data generated between two devices. Incoming messages can also be retrieved in plaintext as shown in Figure 10.33.
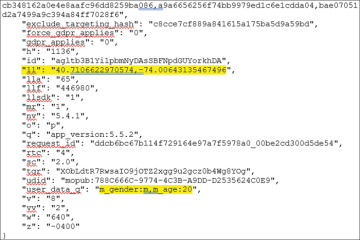
FIGURE 10.31 Mopub banner ad including PII: Age, sex, and exact location
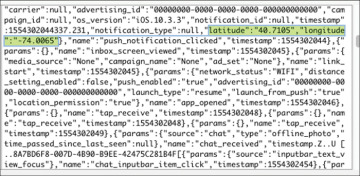
FIGURE 10.32 Latitude/longitude data from greventLog.sqlite
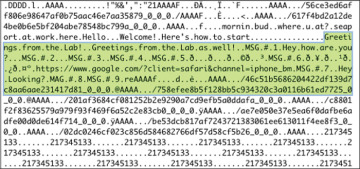
FIGURE 10.33 Text messages extracted in plaintext viewed in Hex Tab (BlackLight)
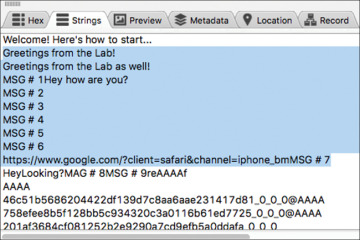
FIGURE 10.34 Text messages in plaintext viewed in Strings tab (BlackLight)
