- Introduction
- How Seriously Should You Take Threats to Network Security?
- Identifying Types of Threats
- Assessing the Likelihood of an Attack on Your Network
- Basic Security Terminology
- Concepts and Approaches
- How Do Legal Issues Impact Network Security?
- Online Security Resources
- Summary
- Test Your Skills
Concepts and Approaches
The approach you take toward security influences all subsequent security decisions and sets the tone for the entire organization’s network security infrastructure. Before we delve into various network security paradigms, let us take a moment to examine a few concepts that should permeate your thinking about security.
The first concept is the CIA triangle. This does not refer to clandestine operations involving the Central Intelligence Agency; rather, it is a reference to the three pillars of security: confidentiality, integrity, and availability. When you are thinking about security, your thought processes should always be guided by these three principles. First and foremost, are you keeping the data confidential? Does your approach help guarantee the integrity of data? And does your approach still make the data readily available to authorized users?
While the CIA triangle is a staple of all security courses and certifications, more sophisticated models have been developed. A multi-faceted approach to describing security is found in The McCumber cube. The McCumber cube is a way of evaluating security of a network, looking at all aspects. It was described in detail in 2004 in the book Assessing and Managing Security Risk in IT Systems: A Structured Methodology. It looks at security as a three-dimensional cube. The dimensions are goals, information states, and safeguards. The McCumber cube has the advantage of being a natural expansion of the CIA triangle into three dimensions. This is advantageous because the CIA triangle is widely known and understood in the cyber-security community. This makes the transition to the McCumber cube, and subsequently a taxonomy based on the McCumber cube, easier. Any taxonomy must be readily learned and applied by security professionals in order to be effective. You can see the McCumber cube in Figure 1.1:
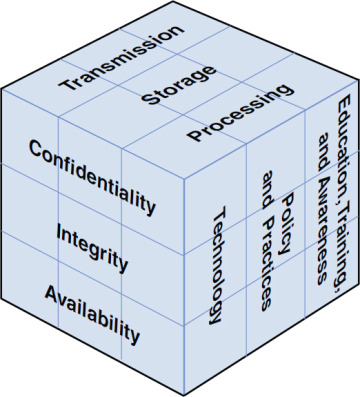
Figure 1.1 The McCumber cube
Another important concept to keep in mind is least privileges. This means that each user or service running on your network should have the least number of privileges/access required to do her job. No one should be granted access to anything unless it is absolutely required for the job.
Network security paradigms can be classified based on either the scope of security measures taken (perimeter, layered) or how proactive the system is.
In a perimeter security approach, the bulk of security efforts are focused on the perimeter of the network. This focus might include firewalls, proxy servers, password policies, or any technology or procedure to make unauthorized access of the network less likely. Little or no effort is put into securing the systems within the network. In this approach, the perimeter is secured, but the various systems within that perimeter are often vulnerable.
There are additional issues regarding perimeter security that include physical security. These issues can include fences, closed-circuit TV, guards, locks, and so on, depending on the security needs of the organization.
The perimeter approach is clearly flawed, so why do some companies use it? Small organizations might use the perimeter approach if they have budget constraints or inexperienced network administrators. A perimeter method might be adequate for small organizations that do not store sensitive data, but it rarely works in a larger corporate setting.
A layered security approach is one in which not only is the perimeter secured, but individual systems within the network are also secured. All servers, workstations, routers, and hubs within the network are secure. One way to accomplish this is to divide the network into segments and secure each segment as if it were a separate network, so if the perimeter security is compromised, not all the internal systems are affected. This is the preferred method and should be used whenever possible.
You should also measure your security approach by how proactive/reactive it is. This is done by gauging how much of the system’s security infrastructure and policies are dedicated to preventive measures and how much of the security system is designed to respond to attack. A passive security approach takes few or no steps to prevent an attack. A dynamic or proactive defense is one in which steps are taken to prevent attacks before they occur.
One example of this defense is the use of IDSs, which work to detect attempts to circumvent security measures. These systems can tell a system administrator that an attempt to breach security has been made, even if that attempt is not successful. IDSs can also be used to detect various techniques intruders use to assess a target system, thus alerting a network administrator to the potential for an attempted breach before the attempt is even initiated.
In the real world, network security is usually not completely in one paradigm or another; it is usually a hybrid approach. Networks generally include elements of both security paradigms. The two categories also combine. One can have a network that is predominantly passive but layered or one that is primarily perimeter but proactive. It can be helpful to consider approaches to computer security along a Cartesian coordinate system, as illustrated in Figure 1.2, with the x axis representing the level of passive–active approaches and the y axis depicting the range from perimeter to layered defense.
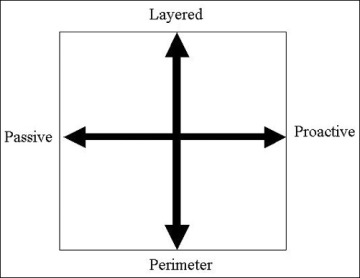
Figure 1.2 The security approach guide.
The most desirable hybrid approach is a layered paradigm that is dynamic—that is, in the upper-right quadrant of the figure.
