- "Do I Know This Already?" Quiz
- Physical Security Measures
- Logical Security Concepts
- Wireless Security Protocols and Authentication
- Malware Removal and Prevention
- Social Engineering Threats and Vulnerabilities
- Microsoft Windows OS Security Settings
- Security Best Practices to Secure a Workstation
- Securing Mobile Devices
- Data Destruction and Disposal
- Configuring Security on SOHO Networks
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Security Best Practices to Secure a Workstation
220-1002: Objective 2.7: Given a scenario, implement security best practices to secure a workstation.
Secure workstations are the foundation of secure networks. If an outside hacker or thief can access a workstation, the whole network may be compromised. The following sections cover use of passwords, account management, and other methods to make workstations secure.
Password Best Practices
Not all passwords are equally secure, and some are very easy to hack. It is important that administrators use stringent security policy settings to require users to follow strict guidelines for password they use to access the network. The guidelines in the following sections reflect password best practices.
Setting Strong Passwords
Guidelines for setting strong passwords should include requirements for minimum length and a mixture of alphanumeric and symbol characters. Every extra character in a password makes it much harder to hack. Using a password generator can make the creation of strong passwords easier. For example, the Norton Identity Safe Password Generator (https://identitysafe.norton.com/password-generator) offers highly customizable random passwords and can generate multiple passwords at the same time.
Password Expiration
No matter how strong a password is, it becomes less secure over time. The longer it is in use, the more susceptible it is to social engineering, brute forcing, or other attacks. The risk of password discovery by unauthorized users is minimized by the use of a password expiration policy under which passwords expire after a particular length of time and must be reset.
Screensaver Required Password
To help protect computers from unauthorized use, users can be required to enter their password to return to the desktop after the screensaver appears. Users should also be required to lock their workstations so that a logon is required to return to the desktop. (See “Timeout/Screen Lock,” later in this chapter, for details.)
In Windows, the screensaver required password setting (On Resume, Display Logon Screen check box) is located in the Screen Saver Settings window, which can be accessed from Settings > Personalization in Windows 10. In macOS, use the Desktop & Screen Saver menu to choose a screen saver and Security & Privacy to require a password to unlock the system.
BIOS/UEFI Passwords
BIOS/UEFI passwords prevent unauthorized users from changing settings. Note that they can be removed by resetting the CMOS. Some motherboards feature a jumper block or a push button to reset the CMOS. If this feature is not present, the CMOS can be reset by removing the CMOS battery for several minutes. Configuration of BIOS/UEFI security settings is covered in more detail in Chapter 3, “Hardware.”
Requiring Passwords
PC users should be trained to use passwords to secure their user accounts. Administrators can require this through the Local Security Policy and Group Policy in Windows.
Passwords can be set up to require users to do the following:
Change passwords periodically to keep them fresh and secure.
Be informed in advance that passwords are about to expire so that users can change passwords early and prevent being locked out at an inconvenient time.
Enforce a minimum password length to keep passwords strong.
Require complex passwords that include a mixture of letters, numbers, and special characters.
Prevent old passwords from being reused continually by tracking past passwords and not allowing them.
Wait a certain number of minutes after a specified number of unsuccessful logins has taken place before being able to log in again.
To create a password or adjust password settings in Windows 10, go to Settings > Accounts > Sign-in Options. To change or enforce password policy settings, go to the following location by using the Group Policy Management Console: Computer Configuration > Windows Settings > Security Settings > Account Policies > Password Policy. Figure 7-14 shows the path to these settings.
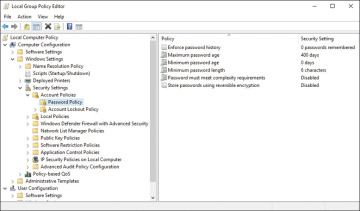
FIGURE 7-14 Password Policy Settings
Account Management
User account settings, when combined with workstation security settings, help prevent unauthorized access to the network. The account management settings described in the sections that follow can enhance security.
Restricting User Permissions
User permissions for standard users prevent systemwide changes, but additional restrictions can be set with Group Policy or Local Security Policy.
Login Time Restrictions
To prevent a user account from being used after hours or before the start of business, login time restrictions can be used to specify when an account can be used.
Disabling Guest Account
The guest account in Windows is a potential security risk, so it should be disabled. If visitors need Internet access, a guest wireless network that doesn’t connect to the business network is a good replacement.
Failed Attempts Lockout
Password policy should specify that a user should be locked out after a specified number of failed attempts to log into an account. A lockout policy can also incorporate a timeout policy, which specifies how long the user must wait after an unsuccessful login before attempting to log in again.
Timeout/Screen Lock
Automatic screen locking can be configured to take effect after a specified amount of idle time, which can help safeguard a system if a user forgets to lock the system manually. Before screen locking can be used, accounts must have the screen lock feature enabled. In Windows 10, go to Settings > Personalization > Lock Screen.
In Windows, users can lock their screens manually by pressing Windows+L on the keyboard or pressing Ctrl+Alt+Del and selecting Lock Computer. In Linux, the keys to use vary by desktop environment. In macOS, use Ctrl+Shift+Eject or Ctrl+Shift+Power (for keyboards without the Eject key).
Changing Default Usernames and Passwords
Default usernames and passwords for SOHO routers or other devices or services that have default passwords should be changed. Default usernames and passwords are available in documentation for these devices, so it is easy for an attacker to find the defaults and use them to take over routers or other devices that are still set to the default passwords.
Basic Active Directory Functions
Active Directory (AD) functions occur in the Windows Server environment, not on local workstations. A full discussion of Active Directory is well beyond the scope of the CompTIA A+ exam, but understanding the essentials of user accounts is necessary because user access issues are a common for support personnel. If a support technician has access to Active Directory, basic user account functions can be performed in the Microsoft Management Console (MMC) or by navigating to the Active Directory Users and Computers folder. This second method is used in Figure 7-12, which shows an account being created.
Creating, Deleting, Resetting/Unlocking, and Disabling an Account
To create an account, select Action > New > User (or right-click the Users folder), as shown in Figure 7-15. Windows opens a dialog where you now enter the new user’s account information, as shown in Figure 7-16.
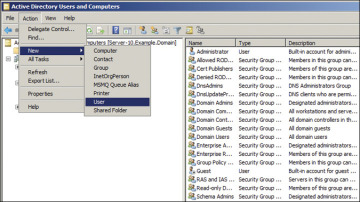
FIGURE 7-15 Creating a New User Account in Active Directory Users and Computers
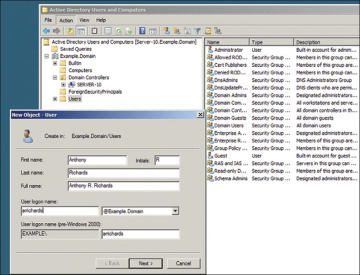
FIGURE 7-16 New User Account
Click the Next button, and an initial password dialog box appears. Figure 7-17 shows this dialog for a new account; note that this dialog allows you to set a password and indicate how the password will be managed by Active Directory.
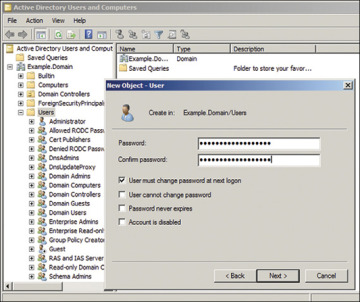
FIGURE 7-17 Initial Password Dialog Box
Click the Next button to create the user.
After a user is created, a technician might need to perform a few common tasks:
Account deletion: A technician might need to completely remove a user from Active Directory.
Password reset/unlock: This may need to be done when a user has forgotten a password or failed to authenticate.
Disable account: It is possible to deactivate a user but keep the account and its records.
These tasks can all be performed by right-clicking on a user’s name. Note that commands for all three of these functions—Delete, Reset Password, and Disable account—appear in the menu in Figure 7-18.
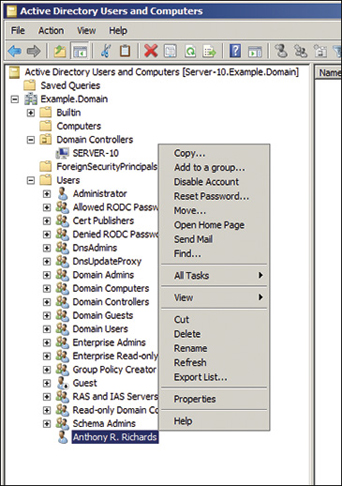
FIGURE 7-18 User options in Active Directory
Disabling Autorun/AutoPlay
Autorun is a feature that enables programs to start automatically when a CD or USB drive or flashcard is connected to a computer. AutoPlay is a similar feature with enhanced options in a Windows environment. Both Autorun and AutoPlay allow the user to be selective in what kinds of programs, updates, and syncs can take place. When you disable autorun, an optical disc or USB drive won’t automatically start its autorun application (if it has one), and any embedded malware won’t have a chance to infect the system before you scan the media. AutoPlay is a similar feature that pops up a menu of apps to use for the media on an optical drive or USB flash drive.
The easiest way to turn off AutoPlay in Windows 10 is to open the AutoPlay applet in Settings > Devices > AutoPlay and toggle the button off. Figure 7-19 shows the AutoPlay Settings window in Windows 10. Figure 7-20 shows how to turn off AutoPlay from the Group Policy settings.
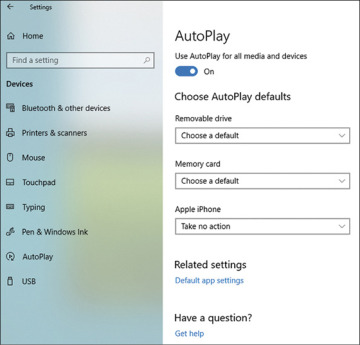
FIGURE 7-19 AutoPlay Settings in Windows 10
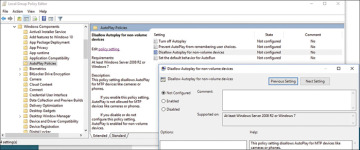
FIGURE 7-20 Disabling Autoplay in the Group Policy Settings
To disable autorun in Windows by using Local Group Policy, complete the following steps:
Step 1. Click Start and in the search field type gpedit.msc to open the Local Group Policy Editor.
Step 2. Navigate to Computer Configuration > Administrative Templates > Windows Components > AutoPlay Policies.
Step 3. Double-click the Turn Off AutoPlay setting to display the Turn Off AutoPlay configuration window.
Step 4. Click the Enabled radio button and then click OK to enable the policy named Turn off AutoPlay.
For security reasons, macOS does not support any type of autorun feature, but it is possible to select apps you want to run on startup. To edit this list, select Apple menu > System Preferences > Users and Groups > Login Items.
In Linux, you can disable autorun on systems that use the Nautilus file manager by changing the properties on the Media tab to enable Never Prompt or Start Programs on Media Insertion and disable Browse Media When Inserted.
Using Data Encryption
Data encryption should be used on laptops and other systems that might be used outside the more secure corporate network environment. Laptops containing unencrypted sensitive data have led to many data breaches. To encrypt folders or drives, use the following steps:
Step 1. Right-click the folder or drive to be secured and select Properties.
Step 2. Click the Advanced button at the bottom of the General tab.
Step 3. In the Advanced Attributes dialog, select the Encrypt Contents to Secure Data check box and click OK.
These steps are shown in Figure 7-21, where a folder named A+ is being encrypted.

FIGURE 7-21 Encrypting Files or Drives
Patch/Update Management
Patches and updates to operating systems and applications should be managed centrally to prevent systems from falling out of compliance. Microsoft’s Windows Server Update Services (WSUS) can be used for OS and application patches and updates for Microsoft products. macOS Server’s Software Update service provides the same role for macOS machines. Linux distributions use various programs to manage updates.
