- "Do I Know This Already?" Quiz
- Physical Security Measures
- Logical Security Concepts
- Wireless Security Protocols and Authentication
- Malware Removal and Prevention
- Social Engineering Threats and Vulnerabilities
- Microsoft Windows OS Security Settings
- Security Best Practices to Secure a Workstation
- Securing Mobile Devices
- Data Destruction and Disposal
- Configuring Security on SOHO Networks
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Microsoft Windows OS Security Settings
220-1002: Objective 2.6: Compare and contrast the differences of basic Microsoft Windows OS security settings.
Microsoft has made several security settings and tools available in the Windows OS. These settings and tools allow users and administrators to control access to files, folders, printers, and physical locations.
The sections that follow discuss the purposes and principles of access control through:
Users and groups
NTFS vs. share permissions
Shared files and folders
System files and folders
User authentication
Run as administrator vs. standard user
BitLocker
BitLocker To Go
EFS
Users and Groups
Users in Windows can be assigned to different groups, each with different permissions. The Local Policy settings (for local PCs) and Group Policy settings (for networked PCs connected to a domain controller running Active Directory) can restrict PC features by group or by PC. The 220-1002 exam covers some of the differences between the accounts. There are three standard account levels in Windows:
Standard user: Standard accounts have permission to perform routine tasks. However, these accounts are blocked from performing tasks that involve systemwide changes, such as installing hardware or software, unless they can provide an administrator password when prompted by User Account Control (UAC).
Administrator: Users with an administrator account can perform any and all tasks.
Guest: The guest account level is the most limited. A guest account cannot install software or hardware or run already-existing applications and cannot access files in shared document folders or the Guest profile. The Guest account is disabled by default. If it is enabled for a user to gain access to the computer, that access should be temporary, and the account should be disabled again when the user no longer requires access.
In Windows versions up to 8.1, the power users account is a specific account type that has more permissions than standard users but fewer than administrators. In those versions, power users have the same rights and permissions as standard users, but a custom security template can be created if the Power Users group needs specific permissions, such as for the operation of legacy programs.
In Windows 10 the Power Users group has been discontinued, but it is available to assign for backward compatibility.
NTFS vs. Share Permissions
Microsoft introduced New Technology File System (NTFS) as an improved way to store files on disks over the FAT system of Windows 95. The changes in storage systems allowed for implementing file security in the form of permissions. Permissions control both local and network access to files and can be set for individual users or groups.
Allow vs. Deny
Each permission has two settings: Allow or Deny. Generally, if you want a user to have access to a folder, you add that user to the list and select Allow for the appropriate permission. If you don’t want to allow a user access, normally you simply don’t add the user to a list. In some cases, an administrator must issue an explicit denial if the user is part of a larger group that already has access to a parent folder but needs to be kept out of a particular subfolder.
Moving and Copying Folders and Files
Moving and copying folders and files have different results depending on permissions. For example, when you copy a folder or file to a different volume, the folder or file inherits the permissions of the parent folder it was copied to (the target directory). When you move a folder or file to a different location on the same volume, the folder or file retains its original permissions.
File Attributes
File attributes are used in Windows to indicate how files can be treated. They can be used to specify which files should be backed up, which should be hidden from the normal GUI or command-line file listings, whether a file is compressed or encrypted, and so on, depending on the operating system.
To view file attributes in Windows, right-click a file in File Explorer or Windows Explorer and select Properties. To view file attributes from the Windows command line, use the Attrib command.
Shared Files and Folders
Shared files and folders have their permissions assigned via the Security tab of the object’s properties sheet. Folder and file permissions vary by user type or group and can include the following:
Full control: Complete access to the contents of the file or folder. When Full Control is selected, all of the following are selected and enabled automatically.
Modify: Change file or folder contents.
Read & Execute: Access file or folder contents and run programs.
List Folder Contents: Display folder contents.
Read: Access a file or folder.
Write: Add a new file or folder.
Administrative Shares vs. Local Shares
Local shares are normally configured on a folder or library basis in Windows. However, Windows sets up special administrative shares that are available across a network for each local drive. For example, the administrative share for the C: drive on a system called MARK-PC is \\MARK-PC\C$.
To connect to the administrative share, a user must provide a username and password for an account on that system.
Permission Inheritance and Propagation
Permission propagation and inheritance describe how files and folders receive permissions.
If you create a folder, the default action is for the folder to inherit permissions from the parent folder—that is, any permissions that you set in the parent will be inherited by any subfolder of the parent. To view an example of this, locate any folder within an NTFS volume (besides the root folder), right-click it and select Properties, access the Security tab, and then click the Advanced button. In Windows 8/8.1/10, the Advanced Security Settings dialog offers these buttons: Add, Remove, View, and Disable Inheritance.
You can also propagate permission changes to subfolders that are not inheriting from the current folder. To do so, select Replace All Child Object Permissions with Inheritable Permissions from This Object. Remember that folders automatically inherit from the parent unless you turn off inheritance, and you can propagate permission entries to subfolders at any time by selecting the Replace option.
System Files and Folders
System files and folders are files and folders with the system(s) attribute. They are normally not displayed in File Explorer to help protect them from deletion.
To make these files and folders visible in Windows 10:
Step 1. Open File Explorer.
Step 2. In the top left select the View tab.
Step 3. Uncheck the boxes that are hidden that need to be viewed.
Figure 7-12 depicts the File Explorer boxes that hide files.

FIGURE 7-12 Showing Hidden Files in Windows 10
User Authentication
Authentication is the process of securely determining that authorized persons accessing computers or network are who they say they are. Windows includes a variety of authentication protocols that can be used on a corporate network, including Kerberos, TLS/SSL, PKU2U, and NTLM.
Apple, Microsoft, and Google use mutual authentication for multiple services (also known as SSO or Single Sign-on) to enable a single login that provides access to multiple services. For example, a single Microsoft Account login provides access to Outlook email, the Microsoft Store, and OneDrive. To make SSO possible in Windows, client IP addresses are mapped to usernames in Windows Active Directory. Similarly, a single Apple login provides access to iTunes, iCloud, and other services. A single Google login provides access to Gmail, Google Drive, and other services.
BitLocker and BitLocker To Go
To encrypt an entire drive, you need some kind of full disk encryption software. Several options are currently available on the market; one option developed for business-oriented versions of Windows by Microsoft is called BitLocker. This software can encrypt the entire disk, which, after completed, is transparent to the user. However, there are some requirements for this, including:
A Trusted Platform Module (TPM) chip, which is a chip residing on the motherboard that actually stores the encrypted keys.
or
An external USB key to store the encrypted keys. Using BitLocker without a TPM chip requires changes to Group Policy settings.
and
A hard drive with two volumes, preferably created during the installation of Windows. One volume is for the operating system (most likely C:), and it will be encrypted; the other is the active volume, and it remains unencrypted so that the computer can boot. If a second volume needs to be created, the BitLocker Drive Preparation Tool can be of assistance; it can be downloaded from the Microsoft Download Center.
BitLocker software is based on Advanced Encryption Standard (AES) and uses a 128-bit encryption key.
Since Windows Vista SP1, it has been possible to use BitLocker to encrypt internal hard disk volumes other than the system drive. For example, if a hard disk is partitioned as C: and D: drives, BitLocker can encrypt both drives.
Windows 10 has several enhancements that allow BitLocker to be more user friendly, but the essentials of BitLocker are the same as in Windows 7.
BitLocker To Go
In Windows 7 and later versions, BitLocker functionality is extended to removable drives and external USB drives (including flash drives) with BitLocker To Go.
To enable BitLocker on Windows 10, go to the Control Panel > System and Security > BitLocker Drive Encryption. For external drives, simply right-click the drive to encrypt and select Enable BitLocker to start the encryption process. During the process, you are prompted to specify a password or a smart card for credentials to access the drive’s contents.
EFS
Business-oriented editions of Windows include support for Encrypting File System (EFS). EFS can be used to protect sensitive data files and temporary files and can be applied to individual files or folders. (When EFS is applied to folders, all files in an encrypted folder are also encrypted.)
EFS files can be opened only by the user who encrypted them, by an administrator, or by EFS keyholders (users who have been provided with the EFS certificate key for another user’s account). Thus, they are protected against access by hackers.
Files encrypted with EFS are listed with green filenames when viewed in Windows Explorer or File Explorer. Only files stored on a drive that uses NTFS can be encrypted.
To encrypt a file in Windows 10, follow this process:
Step 1. Right-click the file in File Explorer and select Properties.
Step 2. Click the Advanced button on the General tab.
Step 3. Click the empty Encrypt Contents to Secure Data check box. Figure 7-13 shows the steps for EFS encryption.
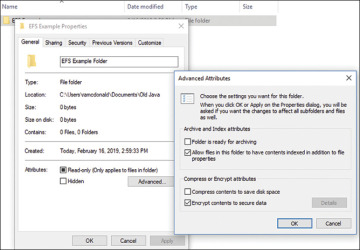
FIGURE 7-13 EFS Encryption Steps
Step 4. Click OK.
Step 5. Click Apply. When prompted, select the option to encrypt the file and parent folder or only the file as desired and click OK.
Step 6. Click OK to close the properties sheet.
To decrypt the file, follow the same procedure but clear the Encrypt Contents to Secure Data check box in Step 3.
