- "Do I Know This Already?" Quiz
- Physical Security Measures
- Logical Security Concepts
- Wireless Security Protocols and Authentication
- Malware Removal and Prevention
- Social Engineering Threats and Vulnerabilities
- Microsoft Windows OS Security Settings
- Security Best Practices to Secure a Workstation
- Securing Mobile Devices
- Data Destruction and Disposal
- Configuring Security on SOHO Networks
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Social Engineering Threats and Vulnerabilities
220-1002: Objective 2.5: Compare and contrast social engineering, threats, and vulnerabilities.
Botnets have made hacking so easy that any network can be tested by hackers thousands of times per day. Updated antivirus/anti-malware software and other software does the heavy lifting in protecting networks and devices. But another constant threat to a computer network is users being manipulated or tricked into doing hackers’ work for them. This hacking technique is known as social engineering. The following sections describe social engineering and other threats and vulnerabilities to networks.
Social Engineering
Six common social engineering techniques that all employees in an organization should know about are phishing, spear phishing, impersonation, shoulder surfing, tailgating, and dumpster diving. The sections that follow describe each of these social engineering techniques.
The key to mitigating these social engineering threats is a combination of ensuring employee awareness, implementing policies and protocols for handling sensitive internal information, and, whenever possible, using cybersecurity tools.
Phishing
Phishing involves creating bogus websites or sending fraudulent emails that trick users into providing personal, bank, or credit card information. A variation, phone phishing, uses an interactive voice response (IVR) system that the user has been tricked into calling to dupe the user into revealing information.
Phishing is a constant threat that can be addressed with awareness warnings from administrators that give examples of the latest threats and education for employees about using judgment to identify suspicious messages.
Figure 7-11 illustrates a typical phishing email.
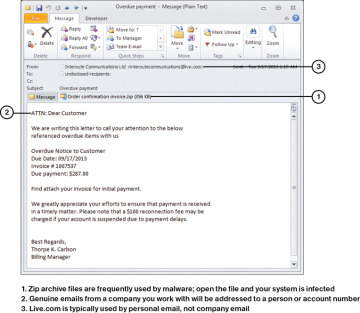
FIGURE 7-11 A Message That Purports to Be About an Overdue Payment but Shows Classic Signs of a Phishing Attack
Spear Phishing
Spear phishing involves sending spoof messages that appear to come from an internal source requesting confidential information, such as payroll or tax information. These attacks typically target a specific person, organization, or business. The best protection against spear phishing is implementing security software that identifies spear phishing mail and educating users about how to handle sensitive information within the organization.
Impersonation
Impersonation is a type of social engineering similar to phishing in which a hacker sends an email pretending to be someone the victim trusts. It can take time and research for the impersonator to figure out how to gain the target’s trust. Impersonation, also known as business email compromise (BEC), is not restricted to email but can happen on the phone or in person. Common sense and strict policies on how to communicate sensitive information can help prevent impersonation attacks.
Shoulder Surfing
Shoulder surfing is the attempt to view physical documents on a user’s desk or electronic documents displayed on a monitor by looking over the user’s shoulder. Shoulder surfers sometimes watch the keyboard to see passwords being entered. Shoulder surfers either act covertly, looking around corners, using mirrors or binoculars, or introduce themselves to the user and make conversation in the hopes that the user will let his or her guard down.
A common protection against shoulder surfing is a special privacy screen that limits the viewing range of a display. Employees should be trained to be aware of others being able to see their screens and to leave screens locked when away from their workstations.
Tailgating
Tailgating occurs when an unauthorized person attempts to accompany an authorized person into a secure area by following that person closely and grabbing the door before it shuts. This is usually done without the authorized person’s consent, and sometimes the authorized person is tricked into believing the thief is authorized. If the authorized person is knowingly involved, it is known as piggybacking. Mantraps, mentioned earlier, are designed to thwart tailgating.
Dumpster Diving
Going through the trash seeking information about a network—or a person with access to the network—is called dumpster diving. This type of activity doesn’t have to involve an actual dumpster, of course—just someone searching for any information that will help him or her socially engineer a way into a network. To limit the prospects of a dumpster diver, paper shredders or shredding services should be employed to keep available data limited.
DDoS
A distributed denial of service (DDoS) attack occurs when several (up to thousands) of computers have been compromised with special malware that turns them into bots. The bots then get directions from their new master to attack with thousands of requests to a network site. The traffic is so overwhelming that the site is unreachable by normal traffic and is effectively shut down.
DoS
A denial of service (DoS) attack involves one computer attacking a specific target with an overwhelming number of service requests. This is very similar to a DDoS attack but without the bots. The messages coming from one source can still take down a network, at great cost to a business.
Zero-Day
When legitimate software is sold and distributed, it may have security vulnerabilities that are unknown. When the flaws are discovered, the users may put out alerts while the software company who made the software creates a patch. Sometimes hackers watch for those alerts and exploit the vulnerabilities before the patch is installed, hence the term zero day.
Man-in-the-Middle
A man-in-the-middle (MiTM) attack involves the attacker intercepting a connection while fooling the endpoints into thinking they are communicating directly with each other. Essentially, the attacker becomes an unauthorized and undetected proxy or relay point and the attacker uses this position to capture confidential data or transmit altered information to one or both ends of the original connection.
Brute Force
A brute force attack involves cracking passwords by calculating and using every possible combination of characters until the correct password is discovered. The longer the password used, and the greater the number of possible characters in a password, the longer brute forcing will take. One way an administrator can block brute forcing is to set authentication systems to lock after a specified number of incorrect passwords are offered. Longer passwords also aid in the fight against brute force attacks.
Dictionary Attacks
Dictionary attacks involve attempting to crack passwords by trying all the words in a list, such as a dictionary. A simple list might include commonly used passwords such as “12345678” and “password.” Dictionary attacks can be blocked by locking systems after a specified number of incorrect passwords are offered. Requiring more sophisticated passwords that do not include identifiable information such as birthdays or family names is also a strategy that can be employed.
Rainbow Table
A rainbow table is used in an attack in much the same manner as in a brute force attack, but it is more mathematically sophisticated and takes less time. Rainbow tables are precomputed tables that can speed calculations when cracking hashes.
Spoofing
Spoofing is a general term for malware attacks that purport to come from a trustworthy source. Phishing, spear phishing, and rogue antivirus programs are three examples of spoofing.
Non-Compliant Systems
Non-compliant systems are systems that are tagged by a configuration manager application (for example, Microsoft’s System Center Configuration Manager) for not having the most up-to-date security patches installed. Systems that don’t have the most up-to-date security patches are especially vulnerable to attacks. An example of this would be a user attempting to log on to a corporate network with a personal computer that has not been updated to network standards that comply with the corporations specifications.
Zombie/Botnet
A zombie/botnet is a computer on the Internet that has been taken over by a hostile program so it can be used for malware distribution or distributed denial of service (DDoS) or other attacks without notification to the regular users of the computer. Many malware attacks attempt to turn targeted computers into zombies on a hostile botnet.
