- "Do I Know This Already?" Quiz
- Physical Security Measures
- Logical Security Concepts
- Wireless Security Protocols and Authentication
- Malware Removal and Prevention
- Social Engineering Threats and Vulnerabilities
- Microsoft Windows OS Security Settings
- Security Best Practices to Secure a Workstation
- Securing Mobile Devices
- Data Destruction and Disposal
- Configuring Security on SOHO Networks
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Malware Removal and Prevention
220-1002: Objective 2.4: Given a scenario, detect, remove, and prevent malware using appropriate tools and methods.
Wireless security has evolved over the past few years to adapt to the increasingly available tools that can be used to hack into a wireless network. An administrator cannot safely install a wireless network using the default settings. The following sections describe the security options available on a wireless network.
Malware
Malicious software, or malware, is software designed to infiltrate a computer system and possibly damage it without the user’s knowledge or consent. Malware is a broad term used by computer professionals to include viruses, worms, Trojan horses, spyware, rootkits, keyloggers, adware, and other types of undesirable software. The sections that follow describe some types of malware in more detail.
Ransomware
Ransomware uses malware to encrypt the targeted computer’s files. The ransom demand might be presented after you call a bogus technical support number displayed by a fake error message coming from the ransomware, or the ransom demand might be displayed onscreen. The ransom must be paid within a specified amount of time, or the files will not be decrypted.
The most famous example of ransomware is the WannaCry virus, which spread throughout the world in 2017. It impacted Windows machines that had not been updated with security patches that would have prevented the spread of the attack.
Trojan
Trojan malware, also known as a Trojan horse, is a malware program disguised as a “gift”—usually popular videos or website links—that trick the user into downloading a virus that might be used to trap keystrokes or transmit sensitive information. Trojans are aptly named for the famous story of the wooden Trojan horse—an apparent gift that hid invading soldiers and allowed them to sneak inside the city gates of Troy.
Keylogger
Keylogger viruses are especially dangerous because they track keystrokes and can capture usernames and passwords of unwitting users. A keylogger can be delivered via a Trojan horse, phishing, or a fake email attachment that the user opens. One way to foil these attacks is to require multifactor authentication because the second authentication factor changes, rendering the stolen password invalid.
Rootkit
A rootkit is a set of hacking tools that makes its way deep into the computer’s operating system or applications and sets up shop to take over the computer. Some rootkits do keylogging, some listen for banking information, and more complex ones can take over a computer completely. A rootkit is a complex type of malware that is difficult to detect and remove with standard malware antivirus software. Sometimes wiping the drive and reinstalling the operating system is the only certain solution.
Virus
Just as biological viruses can infect humans and cause all sorts of different illnesses, computer viruses can infect and damage computers. Virus is a generic term for any malicious software that can spread to other computers and cause trouble. Some are more malicious than others, but all need to be guarded against with antivirus updates. Most virus attacks are spread with human assistance when users fall prey to phishing and carelessly open attachments. (Phishing is discussed later in the chapter.)
Botnet
One danger in not protecting a computer from virus attacks is that it may be taken over and become a “bot”—or robot on a network of infected computers. Hackers can infect multiple computers to form a botnet and then use the infected machines to work together to cause trouble, such as by mounting denial of service attacks or spreading spam. Hackers who install networks of bots sometimes sell access to them to other hackers.
Worm
Worms are different from other viruses in that they are able to self-replicate on computers and push themselves out to other computers. Phishing and other human errors are not required for worms to thrive.
Spyware
Spyware is software that spies on system activities and transmits details of web searches or other activities to remote computers. Getting multiple unwanted pop-up windows when browsing the Internet is a good indicator of spyware. Some of the pop-up windows may show fake security alerts (as shown in Figure 7-4) in the hopes that the user will click on something and then purchase rogue or fake antivirus software or just download more malware. Spyware can possibly cause slow system performance.
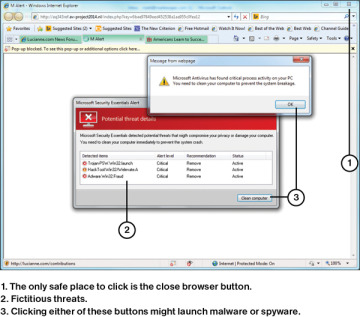
FIGURE 7-4 A Fake Security Alert That Purports to Be from Microsoft
Tools and Methods
The antivirus/anti-malware industry has worked hard to keep pace with the menace of hackers and ever-more-sophisticated viruses. The following sections discuss some of the tools and methods that are used to thwart the hackers.
Antivirus/Anti-malware
Protection against viruses and malware is necessary for every type of computing device, from mobile devices to servers. Computer protection suites that include antivirus, anti-malware, anti-adware, and anti-phishing protection are available from many vendors, but some users prefer a “best of breed” approach and choose the best available product in each category.
Antivirus/anti-malware programs can use some or all of the following techniques to protect users and systems:
Real-time protection to block infection
Periodic scans for known and suspected threats
Automatic updating on a frequent (usually daily) basis
Renewable subscriptions to obtain updated threat signatures
Links to virus and threat encyclopedias
Inoculation of system files
Permissions-based access to the Internet
Scanning of downloaded files and sent/received emails
When attempting to protect against viruses and malware, the most important thing to remember is to keep your anti-malware application up to date. The second most important item is to watch out for is unknown data, whether it comes via email, USB flash drive, mobile device, or some other mechanism.
Recovery Console
The Recovery Console allows you to reset your PC or boot from a recovery disk. If resetting the PC is not sufficient, you can boot from a recovery disk to remove some infected files and restore your original files. Access the recovery tools in Windows 10 by going to Settings > Update & Security > Recovery. Figure 7-5 shows the recovery tools page in Windows 10.
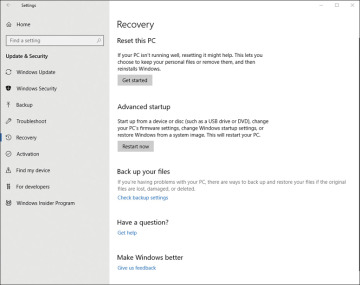
FIGURE 7-5 Windows 10 Recovery Options
Backup/Restore
Troubleshooting an infected PC can be done from a recovery drive. This is a drive that is created and put aside in case it is needed. The drive allows you to boot into a minimal Safe mode that does not install all applications or services. From this mode, you can remove infected files and reboot the computer to normal condition. Figure 7-6 shows the Windows 10 Backup options, which you access by going to Settings > Update & Security > Backup.
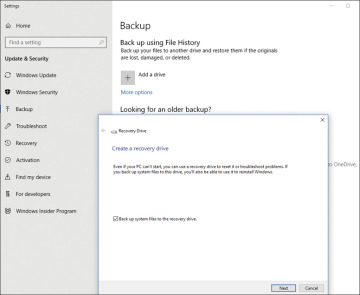
FIGURE 7-6 Tools for Creating a Recovery Drive in Windows 10
Backup/Time Machine
Some Linux distros already have a backup utility installed, and others rely on third-party software. Backing up in Linux can be done by creating a TAR (tape archive) file. macOS includes the Time Machine backup application. Both Linux and macOS must have their backup utilities configured and running in order to be useful in the event that data is lost.
macOS includes Time Machine, a backup utility that can be set up to automatically create daily backups and maintain weekly and monthly versions. To enable and configure Time Machine:
Step 1. Connect a suitable external disk to a macOS system.
Step 2. When prompted, click Use as Backup Disk. You can also check the Encrypt Backup Disk box to protect the backup (see Figure 7-7).
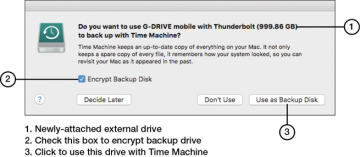
FIGURE 7-7 Selecting an External Disk for Use with Time Machine
Step 3. If you selected the option to encrypt your backup in Step 2, enter a password, confirm it, and enter a password hint. Click Encrypt Disk (see Figure 7-8).
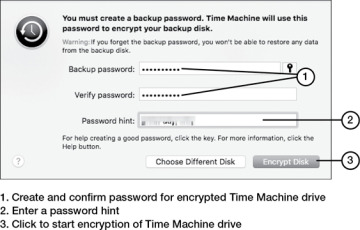
FIGURE 7-8 Encrypting the Time Machine Disk
Step 4. Make sure Time Machine is turned on. After the selected disk is encrypted, the backup starts (see Figure 7-9).
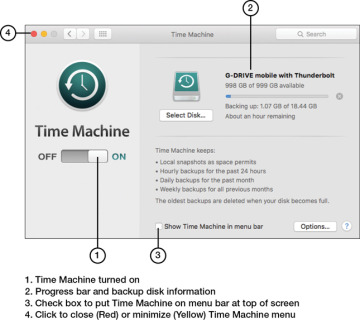
FIGURE 7-9 Creating a Backup with Time Machine
Time Machine is designed to back up user files automatically. However, to create a disk image that can be restored in case of disaster, use Disk Utility.
User Education/AUP (Acceptable Use Policy)
Regardless of the sophistication of physical or digital security measures, the lack of user education and an acceptable use policy (AUP) can lead to security issues. Some elements of a good AUP include the following:
Have users ask for an ID when approached in person by somebody claiming to be from the help desk, the phone company, or a service company.
Have users ask for a name and supervisor name when contacted by phone by someone claiming to be from the help desk, the phone company, or a service company.
Provide contact information for the help desk, phone company, and authorized service companies and ask users to call the authorized contact person to verify that a service call or phone request for information is legitimate.
Ask users to log into systems and then provide the tech the computer rather than giving the tech login information.
Have users change passwords immediately after service calls.
Ask users to report any potential social engineering calls or in-person contacts, even if no information was exchanged. Social engineering experts can gather innocuous-sounding information from several users and use it to create a convincing story to gain access to restricted systems.
Users should be educated in how to do the following:
Keep antivirus, antispyware, and anti-malware programs updated.
Scan systems for viruses, spyware, and malware.
Understand major malware types and techniques.
Scan removable media drives (such as optical discs and USB drives) for viruses and malware.
Disable autorun (as described later in this chapter).
Configure scanning programs for scheduled operation.
Respond to notifications that viruses, spyware, or malware have been detected.
Quarantine suspect files.
Report suspect files to the help desk.
Remove malware.
Disable antivirus software when needed (such as during software installations) and know when to reenable antivirus software.
Avoid opening attachments from unknown senders.
Use anti-phishing features in web browsers and email clients.
Firewalls
Firewalls are used to prevent unauthorized communication into or out of a device or network. Android does not include a firewall, and third-party apps, such as NetGuard, NetStop Firewall, or AFWall+, must be used to provide protection against unwanted Internet traffic. Google Play offers many free firewall apps.
Apple does not include a firewall because the design of iOS uses a feature called “sandboxing” that runs apps in separate protected space.
Windows 10 has incorporated Windows Defender Firewall into the OS. When it is enabled to default settings, Windows Defender Firewall prevents the most common types of malicious traffic into the computer, and the user can customize the settings as needed. Windows Defender is discussed in much greater detail in Chapter 6.
DNS Configuration
Domain Name Service (DNS) involves a database containing public IP addresses and their associated domain names. The purpose of DNS is to translate domain names used in web page requests into IP addresses. Domain name server functions are included in SOHO routers, and in larger networks, a separate domain name server can be used. Domain name servers communicate with other, larger, domain name servers if the requested addresses are not in their databases.
Hackers like to capture DNS information because it provides links between domain names (such as company.com) and IP addresses. With DNS records, a hacker can create false DNS information that can point victims to fake websites and get them to download malware or viruses. Third-party software can provide DNS Security (DNSSEC) that secures a system’s domain name server.
Configuring DNS is covered in Chapter 2, and here we review how the DNS settings are entered when configuring the NIC IPv4 properties. Domain name server addresses can be obtained automatically from the ISP, or they can be statically assigned. Figure 7-10 shows a statically assigned domain name server address and a backup alternative address.
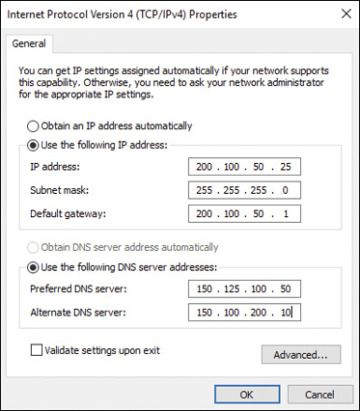
FIGURE 7-10 DNS Addressing Under NIC Properties
