- "Do I Know This Already?" Quiz
- Physical Security Measures
- Logical Security Concepts
- Wireless Security Protocols and Authentication
- Malware Removal and Prevention
- Social Engineering Threats and Vulnerabilities
- Microsoft Windows OS Security Settings
- Security Best Practices to Secure a Workstation
- Securing Mobile Devices
- Data Destruction and Disposal
- Configuring Security on SOHO Networks
- Exam Preparation Tasks
- Review All the Key Topics
- Define Key Terms
- Answer Review Questions
Logical Security Concepts
220-1002: Objective 2.2: Explain logical security concepts.
Because a computer is a combination of physical and logical systems, security practices must address both of these sides of computing. The physical components of security addressed in the previous section are only part of a good security plan and will be ineffective if the security policies stop there. Addressing software (logical) security practices is essential as well.
Active Directory
Active Directory is a Microsoft solution for managing users, computers, and information access in a network. It is based on a database of all resources and users that will be managed within the network. The information in the database determines what people can see and do within the network. Complete understanding of Active Directory is beyond the scope of this course, but every IT support person should know the basics of what it is and how it works. Here are the basics:
Login script: When a user logs onto the network, Active Directory knows who that user is and runs a login script to make the assigned resources available. Examples of login tasks include virus updates, drive mapping, and printer assignments.
Domain: The domain is a computer network or group of computer networks under one administration. Users log into the Active Directory domain to access network resources within the domain.
Group Policy: This is a set of rules and instructions defining what a user or group of users can or cannot do when logged into the domain. You may see the term Group Policy Object (GPO), which is a set of instructions assigned to a group of users or to certain machines on the network.
Organizational Unit (OU): OUs are logical groups that help organize users and computers so that GPOs can be assigned to them. For example, a team of accountants may be assigned to an OU, and their GPO may give them special access to financial records.
Home folder: This folder, which is accessible to the network administrator, is where the user’s data and files are kept locally.
Folder redirection: This allows for the work done by an OU to be saved on a common folder in the domain as directed by the administrator instead of the user. For example, a policy may indicate that all work must be kept in a common folder so all members of a team can see the latest work and updates.
Software Tokens
Like key fobs, mentioned in the previous section for physical security, software tokens are part of a multifactor authentication process. The difference is that software tokens exist in software and are commonly stored on devices.
An example of a software token is Google Authenticator, an app that is downloaded to a device and provides a shared secret key. The user logs in with his or her username and password, and the app runs an authenticating algorithm. This multifactor authentication is more secure than earlier versions of software tokens, which could be stolen.
MDM Policies
Organizations that have many mobile devices need to administer them such that all devices and users comply with the security practices in place. This is usually done with a suite of software known as mobile device management (MDM). The MDM marketplace is quite competitive, and several solutions are available from companies such as VMware (AirWatch), Citrix (XenMobile), and SOTI MobiControl. These products push updates and allow an administrator to configure many mobile devices from a central location. Good MDM software secures, monitors, manages, and supports multiple different mobile devices across the enterprise.
Port Security
Disabling ports refers to using a firewall appliance or software firewall to prevent specified UDP or TCP ports from being used by a service, an application, a specific device, or all devices. Turning off unused ports makes it harder for hackers to find stealthy access into a machine.
MAC Address Filtering
Every network adapter, whether it’s built into a PC, is an add-on card, or is built into a specialized device such as a media adapter or a networked printer, has a unique identifier known as the media access control address, or MAC address. The MAC address (sometimes known as the physical address) is a list of six two-digit hexadecimal numbers. For example, a typical PC MAC address is FA-15-B7-89-6C-24. (MAC addresses are sometimes listed as 12 digits rather than in six groups of 2 digits.)
A MAC address is usually found on a label on the side of a network adapter. If an adapter is already installed, enter ipconfig /all at a command prompt to display the MAC address.
Because MAC addresses are unique, it is possible to control access to most wireless networks by allowing only certain addresses in. The practice of allowing only certain devices is sometimes called whitelisting. Some routers can also be configured to block a list of specified MAC addresses from accessing the wired network.
MAC address filtering can be a useful way to block casual hackers from gaining access to a small wireless (or wired) network, but it can be troublesome for a large network with many different devices coming into and going out of the system as each needs to be entered separately. MAC address filtering is discussed in further detail in Chapter 2, “Networking.”
It is possible to use software to change the MAC address of a network device (a feature sometimes referred to as MAC address cloning). Also, MAC addresses are not encrypted and can be detected by software used to hack networks. Thus, MAC address filtering alone should not be relied on to stop serious attacks.
Certificates
Apps can sometimes hold viruses or other bugs that can cause trouble on a network. It is important to be sure all apps installed come from reliable sources and have been approved by the operating system vendor. App stores for iOS, Android, Windows 8 and later, macOS, and many Linux distros are examples of trusted sources of software.
However, not all software for an operating system comes from an app store. Digital certificates included in software are used to identify the publisher, and most operating systems display warning messages when an app without a digital certificate is being installed. Some settings block the installation of any app that does not have a digital certificate.
In Windows 10 the Certificate Manager keeps track of and check certificates. Figure 7-3 shows the Windows Certificate Manager with specific certificates listed in the right pane. To access Certificate Manager in Windows 10, click the Start button, type certmgr.msc in the search field, and press Enter.
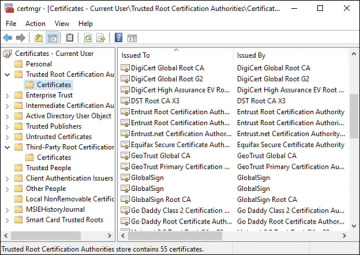
FIGURE 7-3 Certificate Manager
Antivirus/Anti-malware
Just as there is antivirus software for PCs, there is also antivirus/anti-malware software for mobile devices. These are third-party applications that need to be paid for, downloaded, and installed to the mobile device. Some common examples of reliable companies offering antivirus and anti-malware products include McAfee, Norton, and Trend, though many companies offer such products.
iOS works a bit differently from the other mobile operating systems. iOS is a tightly controlled operating system. One of the benefits of being a closed-source OS is that it can be more difficult to write viruses for it, making it somewhat more difficult to compromise. But there is no OS that can’t be compromised, and as Apple’s success has grown, efforts to write viruses for Apple machines have increased. McAfee, Norton, Trend Micro, and others have well-respected iOS protection products.
Firewalls
A firewall is a physical device or a software program that examines data packets on a network to determine whether to forward them to their destination or block them. A firewall can be a one-way firewall, which means it is used to protect against inbound threats only, or it can be a two-way firewall, which protects against both unauthorized inbound and outbound traffic. Most third-party firewall programs, such as ZoneAlarm, are two-way firewalls. A software firewall can be configured to permit traffic between specified IP addresses and to block traffic to and from the Internet except when permitted on a per-program basis.
A corporate network may use a proxy server with a firewall as the sole direct connection between the Internet and the corporate network and use a firewall in the proxy server to protect the corporate network against threats.
Physical firewalls are specialized computers whose software is designed to quickly analyze network traffic and make forwarding decisions based on rules set by the administrator. Over time, that task has been incorporated more and more into software on the computers and into the OS design. An example is Windows Defender Firewall in Windows 10, which is discussed later in the chapter.
Most current operating systems have some sort of firewall built in:
As initially configured, the standard firewall in Windows is a one-way firewall. However, it can be configured to work as a two-way firewall. For more information about how it works, see the section “Firewall Settings,” later in this chapter.
macOS includes an application firewall. In OS X 10.6 and newer, the application firewall offers additional customization options.
Linux, starting with distros based on kernel 2.4.x and later, includes iptables to configure netfilter, its packet-filtering framework. To learn more, see www.netfilter.org. Many distros and third-party Linux apps are available to help make iptables and netfilter easier to configure.
User Authentication/Strong Passwords
Authenticating users means making sure those who are logging in are truly who they say they are. Requiring passwords for user authentication can make systems more secure, but humans have proven pretty lax at voluntarily practicing security. To solve this problem, administrators should mandate strong passwords in their authentication settings.
Strong passwords that foil casual hackers have the following characteristics:
They are at least eight characters long; every character added to this minimum makes the password exponentially safer.
They include a variety of uppercase and lowercase letters, numbers, and symbols.
They do not include real names and words.
Multifactor Authentication
The best type of authentication system is one that uses two or more authentication methods. This is known as multifactor authentication. An example of this would be a person using a smart card and typing a username and password to gain access to a system. The combination of the password and the physical token makes it very difficult for imposters to gain access to a system.
Directory Permissions
Directory permissions is the term used in macOS and Linux for configuring the access levels a user has to a directory (folder) and individual files. In Windows, the equivalent term is file and folder permissions.
In Linux and macOS, directory permissions include:
Read (opens file but no changes)
Write (able to read and change file)
Execute (runs executable file or opens directory)
The chmod command is used in Linux to change directory permissions. In macOS, the Get Info menu’s Sharing & Permissions submenu is used to change directory permissions.
In Windows, file and folder permissions on an NTFS drive include:
Full control
Modify
Read & Execute
List folder contents (applies to folders only)
Read
Write
These settings are configured through the Security tab of the file or folder’s properties sheet. The chmod command and output are discussed in further detail in Chapter 6, “Operating Systems.”
VPN
A virtual private network (VPN) is a private and secure network connection that is carried by an insecure public network, such as the Internet. A VPN connection requires a VPN server at the remote site and a VPN client at the client site. VPN traffic between client and server is encrypted and encapsulated into packets suitable for transmission over the network. VPNs can be used in place of leased lines for connections between locations and for telecommuting workers.
The most common types of VPNs use Point-to-Point Tunneling Protocol (PPTP) and Layer 2 Tunneling Protocol (L2TP/IPsec). Tunneling refers to the practice of using encryption to shield traffic between the client and server from other traffic. PPTP uses 128-bit encryption, and L2TP combined with IPsec (L2TP/IPsec) uses 256-bit encryption. VPNs are discussed further in Chapter 2.
DLP
Data loss/leakage prevention (DLP) involves preventing confidential information from being viewed or stolen by unauthorized parties. DLP goes beyond normal digital security methods such as firewalls and antivirus software by observing and analyzing unusual patterns of data access, email, and instant messaging, whether the data is going into or out of an organization’s network.
Access Control Lists
Access control lists (ACLs) are lists of permissions or restriction rules for access to an object such as a file or folder. ACLs control which users or groups can perform specific operations on specified files or folders.
Smart Card
Smart cards can be used to enable logins to a network, encrypt or decrypt drives, and provide digital signatures when supported by the network server.
Email Filtering
Email filtering can be used to organize email into folders automatically, but from a security standpoint, its most important function is to block spam and potentially dangerous messages.
Email filtering can be performed at the point of entry to a network with a specialized email filtering server or appliance as well as by enabling the spam and threat detection features that are built into email clients or security software.
Spam or suspicious emails can be discarded or quarantined by the user, and false positives that are actually legitimate messages can be retrieved from the spam folder and placed back into the normal inbox.
Trusted/Untrusted Software Sources
As mentioned previously concerning certificates, app stores for iOS, Android, Windows, macOS, and many Linux distros are examples of trusted sources of software. Apps installed from these sources have been approved by the operating system vendor and awarded certificates.
But not all software for an operating system comes from an app store. Digital certificates included in software are used to identify the publisher, and most operating systems display warning messages when an app without a digital certificate is being installed. Some operating systems block the installation of any app that does not have a digital certificate. It is ultimately up to the user to determine the trustworthiness of a software source.
Principle of Least Privilege
Applying the principle of least privilege means giving a user access to only what is required to do his or her job. Most users in a business environment do not need administrative access to computers and should be restricted from functions that could compromise security.
While the principle of least privilege appears to be basic common sense, it should not be taken lightly. When user accounts are created locally on a computer—and especially on a domain—great care should be taken in assigning users to groups. Also, many programs, when installed, ask who can use and make modifications to the program; often the default is “all users.” Some technicians just accept the defaults when hastily installing programs without realizing that they are giving users full control of the program. It is an important practice to give clients all they need but limit their access to only what they need.
